CYBRI mobile penetration testing can help your company reduce the risk of a mobile application breach, improve mobile security, and achieve compliance.
Other report highlights include:
- High-risk vulnerabilities were found in 38 percent of mobile applications for iOS and in 43 percent of Android apps.
- Insecure data storage was identified as the most common vulnerability. This flaw was found in 76 percent of mobile apps and, in some cases, could enable hackers to steal passwords, financial information, personal data, and correspondence.
- Hackers seldom need physical access to a smartphone to steal data: 89 percent of vulnerabilities can be exploited using malware.
- Most cases were caused by weaknesses in security mechanisms (74% and 57% for iOS and Android apps, respectively, and 42% for server-side components).
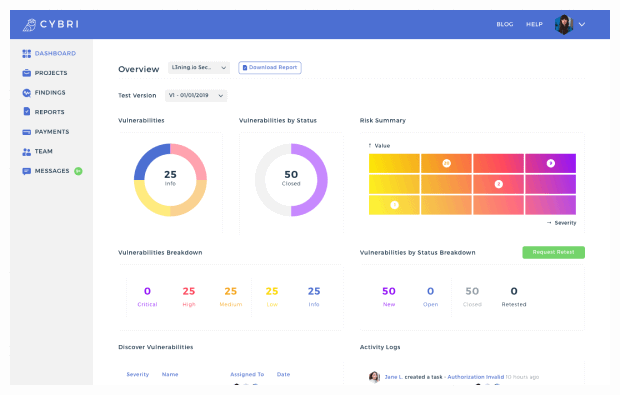
Overview
Mobile App Security
The Top 10 OWASP Mobile Risks
M1: Improper Platform Usage
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M2: Insecure Data Storage
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M3: Insecure Communication
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M4: Insecure Authentication
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M5: Insufficient Cryptography
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M6: Insecure Authorization
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M7: Client Code Quality
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M8: Code Tampering
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M9: Reverse Engineering
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
M10: Extraneous Functionality
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
Methodologies & Scope
Mobile App Testing Phases
1- Planning Phase
— Information Gathering
- Define the scope.
- Search for any publicly available information about the target mobile application
- Mapping: Determine functionality and workflow
- Inventory permissions
2 - Testing Phase
— Conduct Mobile Exploitation Activities
- Authorization: Examine role privilege enforcement and attempt to bypass auth restriction.
- Data: Identify and inventory stored data and encryption.
- Information Disclosure: Examine log files and cache stores
3 - Reporting Phase
- Details on vulnerabilities found, the methodology used, and locations where the problems exist.
Mobile App Pen Testing Features and Benefits
Features of our pen testing services include:
- On-demand testing
- Team collaboration
- Data-rich dashboards
- Clean reports
- Historical data analysis
- Remediation tracking
Benefits of our pen testing services:
- Uncover vulnerabilities in mobile apps
- Test the effectiveness of your defenses
- Spot mistakes made by developers
- Discover bugs in existing applications
Why Choose CYBRI for Your Next Mobile App Penetration Test?
CYBRI Blue Box Technology
We developed our own Blue Box technology, so that collaboration between your organization and our experts is transparent and seamless.
Blue Box features include data-rich dashboards, clean reports, remediation tracking, on-demand testing, and historical data analysis.
Our Red Team experts + CYBRI Blue Box technology won’t let mobile app security threats go undetected.
