HIPAA Penetration Testing
With the deluge of healthcare security incidents and data breaches to information systems last year, mere vulnerability scanning for HIPAA compliance is no longer sufficient. A variety of PCI and HIPAA compliant security policies and assessments like risk analysis, penetration tests, vulnerability scans, security testing, and nontechnical evaluation are regulations that are a requirement for complete protection.
A recent report by HIPAA Journal (December 20, 2019) shows an alarming increase in theft and data breaches across the healthcare landscape. In fact, nearly 39 million healthcare data breaches were reported to the U.S. Department of Health and Human Services (HHS), Office of Civil Rights (OCR) by the end of November 2019. Moreover, this is more than double the number reported in 2018. As a result, HIPAA security controls are clearly insufficient, which makes periodic technical inspection necessary. Therefore, covered entities must ensure they continuously follow HIPAA security rule requirements, security controls, and security measures.
In addition, covered entities that work with a business associate must ensure that the associate has a contract in place that enforces compliance with security rules. Otherwise, gaps in accountability may appear. Furthermore, these associates may also need to participate in HIPAA penetration testing or HIPAA penetration testing programs. Meanwhile, cybercriminals actively exploit vulnerabilities in healthcare data systems. For example, attackers can obtain protected health information such as social security numbers, insurance details, healthcare records, cardholder data, and credit card data. Therefore, maintaining strong confidentiality guarantees for patients is essential.
Trusted by Top Industry Leaders
CYBRI works with companies that are leaders in their industries. In addition, these organizations understand the importance of detecting security threats. As a result, they treat penetration testing as a vital part of their cybersecurity posture.


Benefits of working with CYBRI
All CYBRI Red Team members are U.S.-based, experienced, and highly certified penetration testers.
Easy access to clean and concise reports that can be shared among your executive and technical teams.
We value visibility and transparency. Use our cloud-based platform to follow the pen testing progress and take action as our team detects new vulnerabilities.
HIPAA Penetration Testing Overview
Your organization must be proactive about cybersecurity. Otherwise, cybercriminals can take advantage of weak defenses if they target your systems. In that case, preparation can make the difference between the survival or failure of your business. Think of it as an insurance policy. In particular, cybercriminals know that healthcare organizations cannot afford system downtime. As a result, the consequences of a cyber breach are often catastrophic.
Two questions that healthcare organizations must ask:
- What avenues will cyber criminals pursue to break into my network?
- Will they be successful?

The CYBRI red team conducts HIPAA pen testing through a simulated real-world attack to test your organization’s network for exploitable vulnerabilities. Utilizing a strategic methodology, our Red Team experts will pinpoint the weak areas in your network.
The Red Team will determine:
- The possibility of attack success
- Vulnerabilities that are unidentifiable by automated tools
- Severe vulnerabilities
- The ability of the security controls to detect and defend the attack
- The consequences of a successful attack
CYBRI Red Team?
CYBRI Red Team members are a group of highly vetted US-based ethical hackers. The majority of CYBRI Red Team pen testers are OSCP, GIAC, CISSP, and CEH certified. They use the best testing methodologies in the industry. Hire CYBRI Red Team to expose critical HIPAA vulnerabilities in your organizations web apps, server/host mobile apps, cloud technology, IoT, and API.

Verified identity, background, references, and skills.
Most Red Team members are security professionals that have 10+ years of experience in finding, discovering, and remediating vulnerabilities to help companies gain insight and become more secure from hackers.

The majority of Red Team members are OSCP, GIAC, CISSP, and CEH certified. Many of our members worked in the U.S. Army and at Fortune 500 companies. The complexity and importance of this requires our members to have the utmost expertise which makes them more than qualified to complete a HIPAA penetration test.
HIPAA Pen Testing Compliance Requirements
By law, your organization must remain 100 percent compliant with HIPAA security requirements. However, compliance alone does not eliminate cyber risks, and organizations can still remain vulnerable to cyberattacks. In this context, manual penetration testing helps evaluate the effectiveness of security controls and uncover ePHI vulnerabilities.
For example, the 2019 Cost of a Data Breach Report found that healthcare organizations struggled to retain customers after a data breach due to stolen information. In addition, the industry experienced a customer turnover rate of 7 percent, compared to an average of 3.9 percent in organizations without a breach.
Other highlights from the report include:
- For the ninth year in a row, healthcare organizations had a cost of $6.45 million associated with data and information breaches – over 60 percent higher than the global average of all industries.
- The average cost per breached healthcare record increased to $429 per record – substantially higher than the average of $150 per breached record in other industries.
- It took 236 days for healthcare organizations to identify a breach and an average of 83 days to contain it.
For security and regulatory compliance, penetration testing is considered a best practice for strong cyber hygiene. However, if you do not probe your network, you may never discover insecure, dormant, or unknown systems operating in the shadows of your organization.
In particular, the healthcare industry handles a large volume of valuable PHI data. As a result, protected health information and related vulnerabilities are among the most attractive targets for cybercriminals.
At CYBRI, our Red Team performs custom penetration testing across your organization’s entire infrastructure.
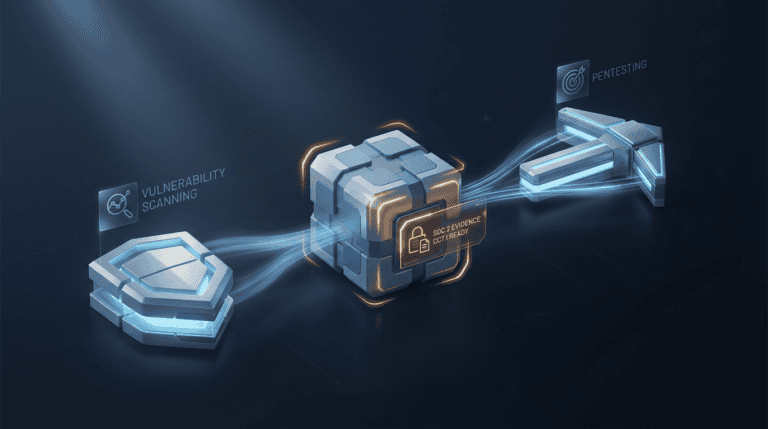
CYBRI Blue Box Technology HIPAA Penetration Test
For security and regulatory compliance, penetration testing is considered a best practice for strong cyber hygiene. However, without regular network probing, organizations may fail to discover insecure, dormant, or unknown systems operating in the shadows of their environment.
In particular, the healthcare industry handles a large volume of valuable PHI data. As a result, protected health information and related vulnerabilities remain among the most attractive targets for cybercriminals.
At CYBRI, our Red Team conducts custom penetration testing across your organization’s entire infrastructure.
The implementation of these procedures and tools is extremely important for healthcare organizations. In addition, any issues discovered during testing are analyzed and addressed, and potential attacker activity is contained to protect the system.
Blue Box features include data-rich dashboards, clean reporting, remediation tracking, on-demand testing, and historical data analysis.
When combined with CYBRI Blue Box technology, our Red Team experts provide a strong solution for continuous security monitoring. As a result, organizations can identify vulnerabilities before cybercriminals exploit them. Furthermore, our experts deliver the validation needed to strengthen confidence in your security posture.
Trusted by Top Industry Leaders


See first-hand how CYBRI can find vulnerabilities within your network.
The global average cost of a data breach in 2019 was $3.92 million. As a result, recovering from a security breach can be financially devastating for many companies. In addition to direct costs, organizations also face regulatory fines, loss of customer trust, and long-term brand reputational damage.
At CYBRI, the Red Team conducts penetration testing through simulated real-world attacks to evaluate your organization’s network for exploitable vulnerabilities. Using a consistent and structured methodology, our experts identify areas where an attacker could gain access to your environment.
In contrast to standard vulnerability scans, CYBRI’s custom penetration testing goes much deeper. It helps detect, identify, and remediate vulnerabilities before cybercriminals can exploit them.
Combined with CYBRI Blue Box technology, our Red Team ensures that network threats do not go undetected. As a result, organizations gain continuous visibility and stronger security assurance.
Assets we test
What to Expect
- Initial pen tester meeting with CYBRI Red Team experts to determine the scope and develop a pen testing plan.
- Threat landscape mapping followed by active intelligence gathering to crack and identify any vulnerabilities, defaults, weaknesses, or misconfigurations.
- Transparency - regular updates and reporting about pen test findings via CYBRI Blue Box platform.
- In-depth findings report with images, descriptions, and vulnerability remedies.
Assessments
Schedule a personalized demo with CYBRI.








Discuss your Project







News & Resources
The implementation of these procedures and tools is extremely important for healthcare organizations. In addition, any issues discovered during testing are analyzed and addressed, and potential attacker activity is contained to protect the system.
Blue Box features include data-rich dashboards, clean reporting, remediation tracking, on-demand testing, and historical data analysis.
When combined with CYBRI Blue Box technology, our Red Team experts provide a strong solution for continuous security monitoring. As a result, organizations can identify vulnerabilities before cybercriminals exploit them. Furthermore, our experts deliver the validation needed to strengthen confidence in your security posture.
The global average cost of a data breach in 2019 was $3.92 million. As a result, recovering from a security breach can be financially devastating for many companies. In addition to direct costs, organizations also face regulatory fines, loss of customer trust, and long-term brand reputational damage.
At CYBRI, the Red Team conducts penetration testing through simulated real-world attacks to evaluate your organization’s network for exploitable vulnerabilities. Using a consistent and structured methodology, our experts identify areas where an attacker could gain access to your environment.
In contrast to standard vulnerability scans, CYBRI’s custom penetration testing goes much deeper. It helps detect, identify, and remediate vulnerabilities before cybercriminals can exploit them.
Combined with CYBRI Blue Box technology, our Red Team ensures that network threats do not go undetected. As a result, organizations gain continuous visibility and stronger security assurance.