Mobile Application Penetration Testing
Coinciding with the rise of mobile phones, hackers target Mobile applications with the specific goal of stealing sensitive information from unsuspecting users. CYBRI’s Mobile application penetration testing services cover all aspects of your app, from user roles, API and web integrations, infrastructure, business logic, and data leakage.
We ensure that each new feature release maintains a strong cybersecurity posture by scheduling your monthly and quarterly pen tests with our easy-to-use BlueBox platform.
What Is Mobile Application Penetration Testing?
Mobile applications interact with your system data and are often the targets for hacking attempts given their wide-spread, easy-to-download nature. Mobile app pen testing can be a complex process as it involves a wide range of variables, differing mobile operating system architectures, and coding language specific parameters.
Benefits Of Working With CYBRI
Work with the nation’s top web app pen testing experts to detect vulnerabilities before hackers do.
U.S.-Based Red Team
All CYBRI Red Team members are U.S.-based, experienced, and highly certified web application penetration testers.
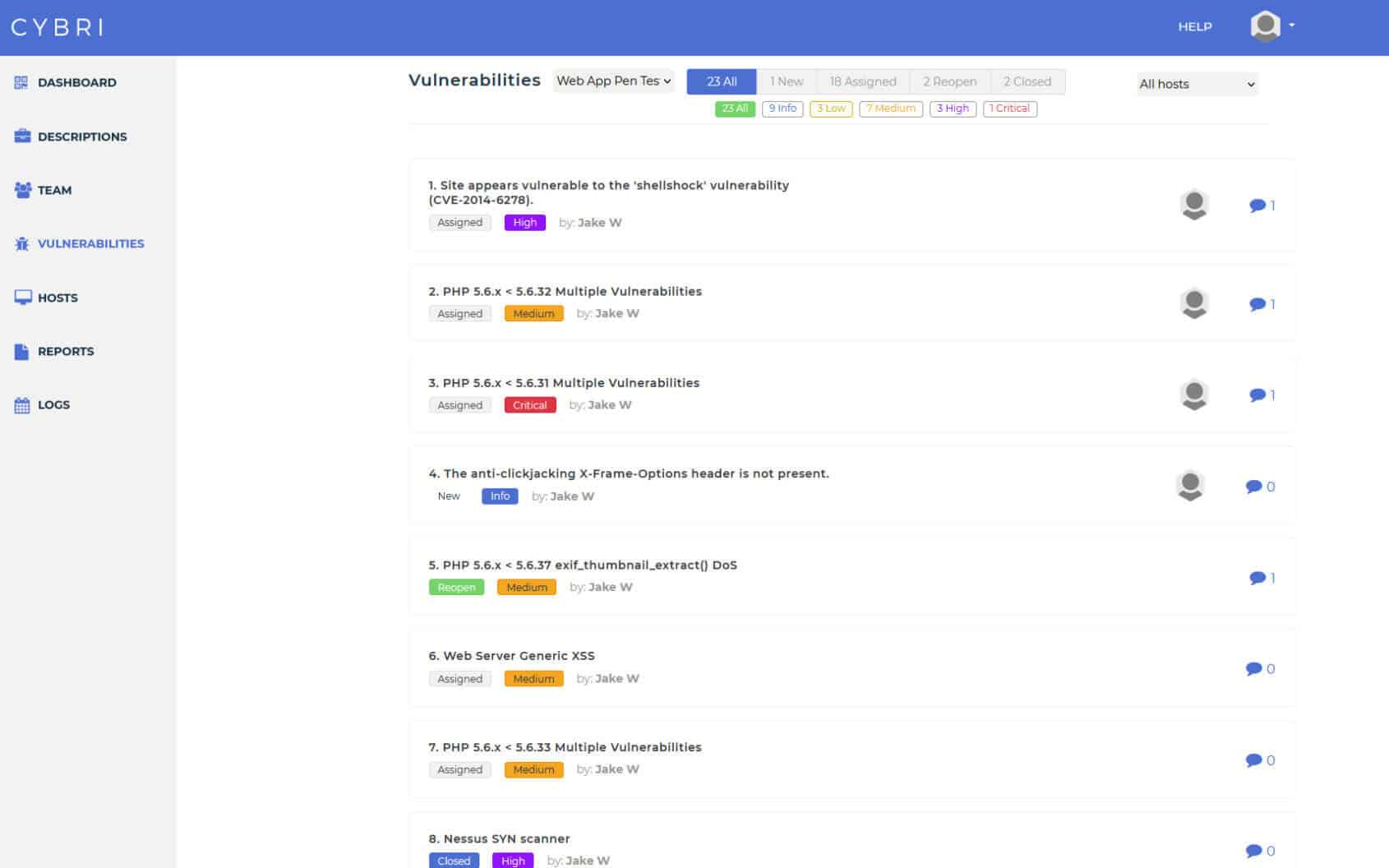
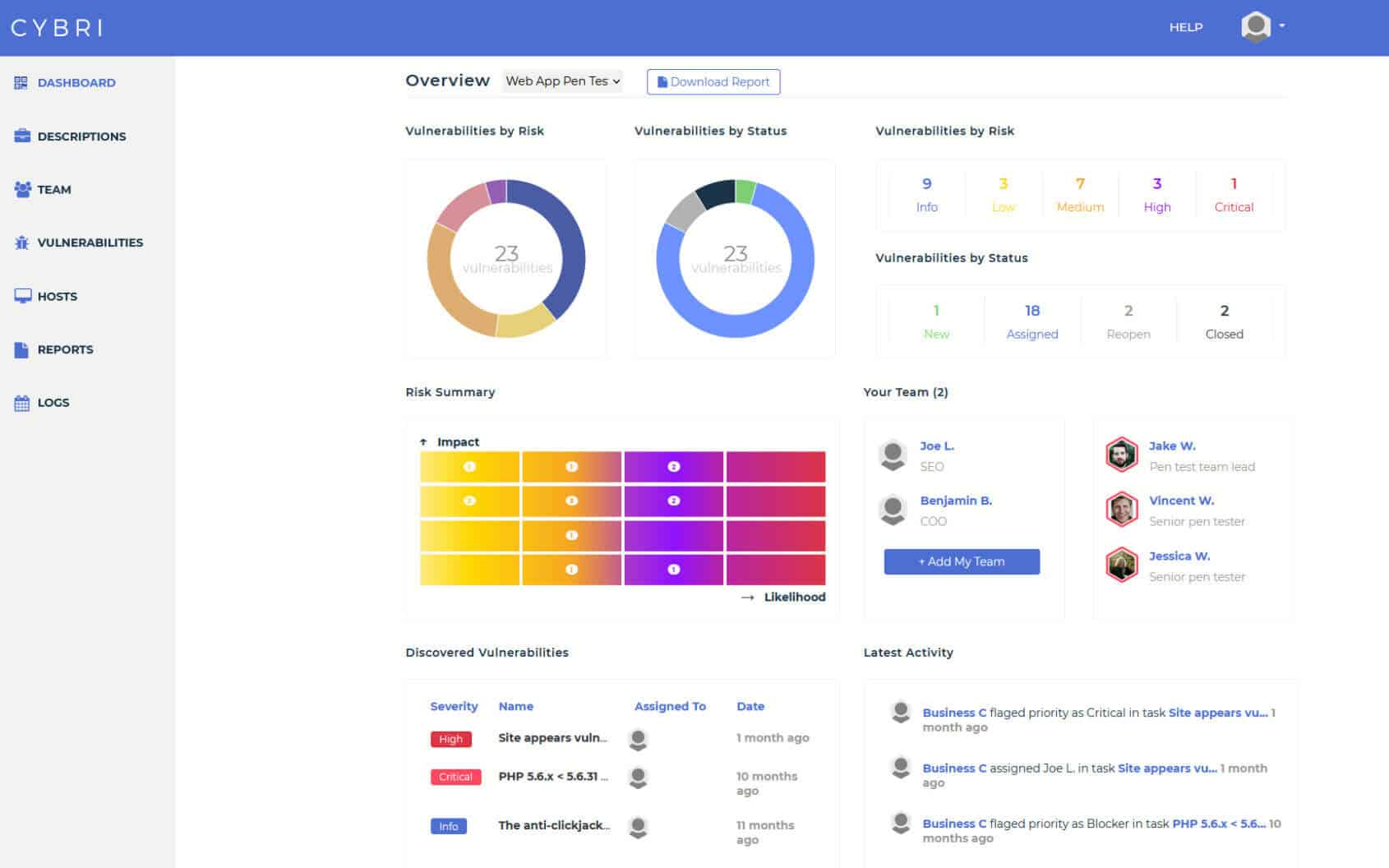
BlueBox Dashboard & Reporting
Easy access to clean and concise web application penetration testing reports that can be shared among your executive and technical teams.
Transparent Process
We value visibility and transparency. Use our cloud-based platform to follow the web application penetration testing progress and take action as our team detects new vulnerabilities.
Maximizing Value Of Mobile Application Penetration Testing
User Role/Authenticated Testing
A highly recommended test for those who don’t pen test frequently and want to uncover as many vulnerabilities as possible. It will have a lot more findings in a shorter period than a Black Box test. We perform a thorough penetration test on your Mobile application from every aspect and each user role using OWASP ASVS, which also includes looking for the OWASP Top 10. This works best for agile teams who update app features frequently.
Data storage and reverse engineering
Our experts will look for artifacts on the mobile platforms that could reveal sensitive data, expose components, or otherwise inform malicious actors as to the nature of the application. This can also be called forensic pen testing, as it leverages digital forensic techniques.
Communication Security Testing
API
API testing is often done in conjunction with Mobile penetration tests. APIs can be a weak vector into any organization that doesn’t check its security. We leverage OWASP’s research to find the most common attack vectors.
Code Review
A code review is the best way to check for vulnerabilities before they are seen by the public. It can also catch business logic flaws and other problems that are not readily apparent in the compiled application. We utilize OWASP’s Code Review Guide and Google’s Standard of Code Review
Black Box/Unauthenticated Testing
What Our Customers Have to Say







Why You Need It:
- Functionality releases – Ensure each release of your application is secure as they get released, as opposed to waiting. Get tested before your release goes public and an attacker can attempt to reverse engineer it.
-
Compliance - Whether you need to comply with:
• SOC2
• HIPAA
• PCI-DSS
or other compliance standards, getting a pen test will help you meet those requirements. - Vendor/Customer Requests - Customers and vendors may require you to perform an application penetration testing to ensure you are secure and showcase that your organization takes the necessary measurements to protect their data. Using our methodology based on OWASP ASVS, OSSTMM, and PTES, we can give them confidence in the results of your test.
- Security Awareness - Pen testing your application will ensure you know where you stand in comparison to industry standards and get the peace of mind you need, such as knowing you have no vulnerabilities in the OWASP Top 10.
- Intrusion Prevention - Application pen testing can reduce your attack surface, which significantly reduces the likelihood of compromise. It is important to ensure that your mobile application is also secure and not a whole into the application backend.
What is manual testing?
The Attack Vectors We Test:
Our mobile penetration testing methodology leverages industry standards such as OWASP’s Mobile Top 10 to look for:
- Improper Platform Usage focuses on the insecure use of the underlying mobile platform, whether it is Android or IOS. This can involve the platform permissions, insecure keychain usage, or other security features.
- Insecure Data Storage is a problem for applications that handle sensitive data, such as PHI or PII. Not securing the data on the mobile device can expose it if the device is stolen or otherwise compromised.
- Insecure Communication can be found by testing how the mobile application communicates with the backend servers. This often focuses on incepting data and trying to decode or downgrade communications.
- Insecure Authentication can be an easy attack to exploit, as it attempts to directly access the mobile application’s backend servers bypassing the app itself and not requiring authentication.
- Insufficient Cryptography relies on accessing the local data in an easy to decrypt form. As mobile apps can store data on a local device, brute force attacks can go unnoticed and weak cryptography can allow malicious actors to see the data.
- Insecure Authorization can also be called privilege escalation as the goal is to take a legitimate user account and gain access to administrative or otherwise privileged areas of the app and sensitive data and functions.
- Client Code Quality are vulnerabilities in the code itself, which can include injection and buffer overflows. They are problems with how the code is implemented and run.
- Code Tampering relies on the malicious actors tricking users into using fake applications, malicious binaries, or otherwise faked resources in order to bypass the applications security. The target can be both local and remote resources and are more common than most people realize as they often go unchecked.
- Reverse Engineering is the attempt to understand how each part of the app works leveraging forensic techniques, especially malware analysis, that looks into the binaries, third-party libraries, and data storage.
- Extraneous Functionality can be exploited by a crafty attacker looking to take advantage of functionality that isn’t necessary or left over from development testing. It often is unnoticed as many features are hidden instead of being disabled.
Agile Pen Testing
What Makes CYBRI One Of The Premier Penetration Testing Companies
Our outstanding penetration testing company services have attracted several clients that range from small startups to huge multinational companies. We are dedicated to improving cybersecurity across the board, which means that our services to your organization continue even after the pen test report has been delivered.
No matter the size of your organization, we will assess all of your cybersecurity needs from scratch to provide security measures tailored to your business needs. Our experts are always available to all of our clients in an advisory capacity should you wish to contact us.
What To Expect During An App Pen Testing:
- Elite services from US-based security experts, who have specialized certifications and expertise in applications
- Hands-on professional advice from our experts to answer your questions and concerns to get the most out of your testing experience
- An expert report that comes in multiple versions for you to distribute appropriately, from an executive summary for management, to a technical report for the developers, or a compliance focused attestation; our clean reports are exactly what you need.
Assessments
What Sets Us Apart
How CYBRI Penetration Testing Works
Discovery
We will collect the needed information from you and your team to make sure that the right assets are being tested and the right team is assigned.
RED TEAM IN ACTION
CYBRI Red Team members will start testing your infrastructure and will ensure coverage of OWASP top 10 vulnerabilities. They will utilize their own techniques to ensure the highest levels and standards of testing.
Reporting
Collaboration
After each finding is verified by our Red Team members, they get submitted into your dashboard and report. Upon completion of each test, you will have a clear report that can be shared with executive and technical members as well as your clients.
Retest
Once the findings have been remediated by your team and the time is right to retest your technology, you can easily do so by scheduling a new test with us or by purchasing an annual package of multiple tests.
Repeat
Improve risk posture and decrease the liability of your organization. Asses the cybersecurity and risk of your organization on an annual engagement basis with the top five percent of the nation’s cybersecurity talent, the CYBRI Red Team.
We spend a week or more preparing before we execute. We will collect the needed information from you and your team to make sure that the right assets are being tested and the right team is assigned.
CYBRI Red Team members will start testing your infrastructure and will ensure coverage of OWASP top 10 vulnerabilities. They will utilize their own techniques to ensure the highest levels and standards of testing.
Communicate with CYBRI Red Team members about your vulnerabilities and assign the vulnerabilities for remediation to your team members; all directly in our platform. Our platform has a clear collaboration functionality to help your team with remediation of the findings.
After each finding is verified by our Red Team members, they get submitted into your dashboard and report. Upon completion of each test, you will have a clear report that can be shared with executive and technical members as well as your clients.
Once the findings have been remediated by your team and the time is right to retest your technology, you can easily do so by scheduling a new test with us or by purchasing an annual package of multiple tests.
Improve risk posture and decrease the liability of your organization. Asses the cybersecurity and risk of your organization on an annual engagement basis with the top five percent of the nation’s cybersecurity talent, the CYBRI Red Team.








Discuss Your Project