Mobile Application Penetration Testing
Mobile applications are prone to security threats and require different setups. CYBRI approaches mobile application security testing (MAST) holistically.
CYBRI uses a blend of static application security testing (SAST) aka, source code analysis, dynamic application security testing (DAST), and forensic techniques to locate mobile-specific issues, vulnerabilities in mobile application code, file analysis, data storage, and network communications.
What is mobile application testing?
Benefits of working with CYBRI
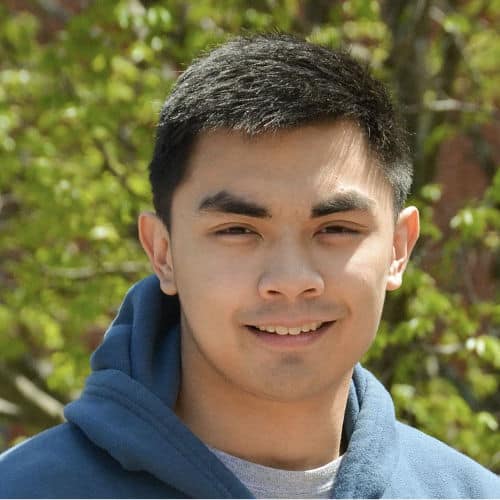
U.S.-Based Red Team
All CYBRI Red Team members are U.S.-based, experienced, and highly certified penetration testers.
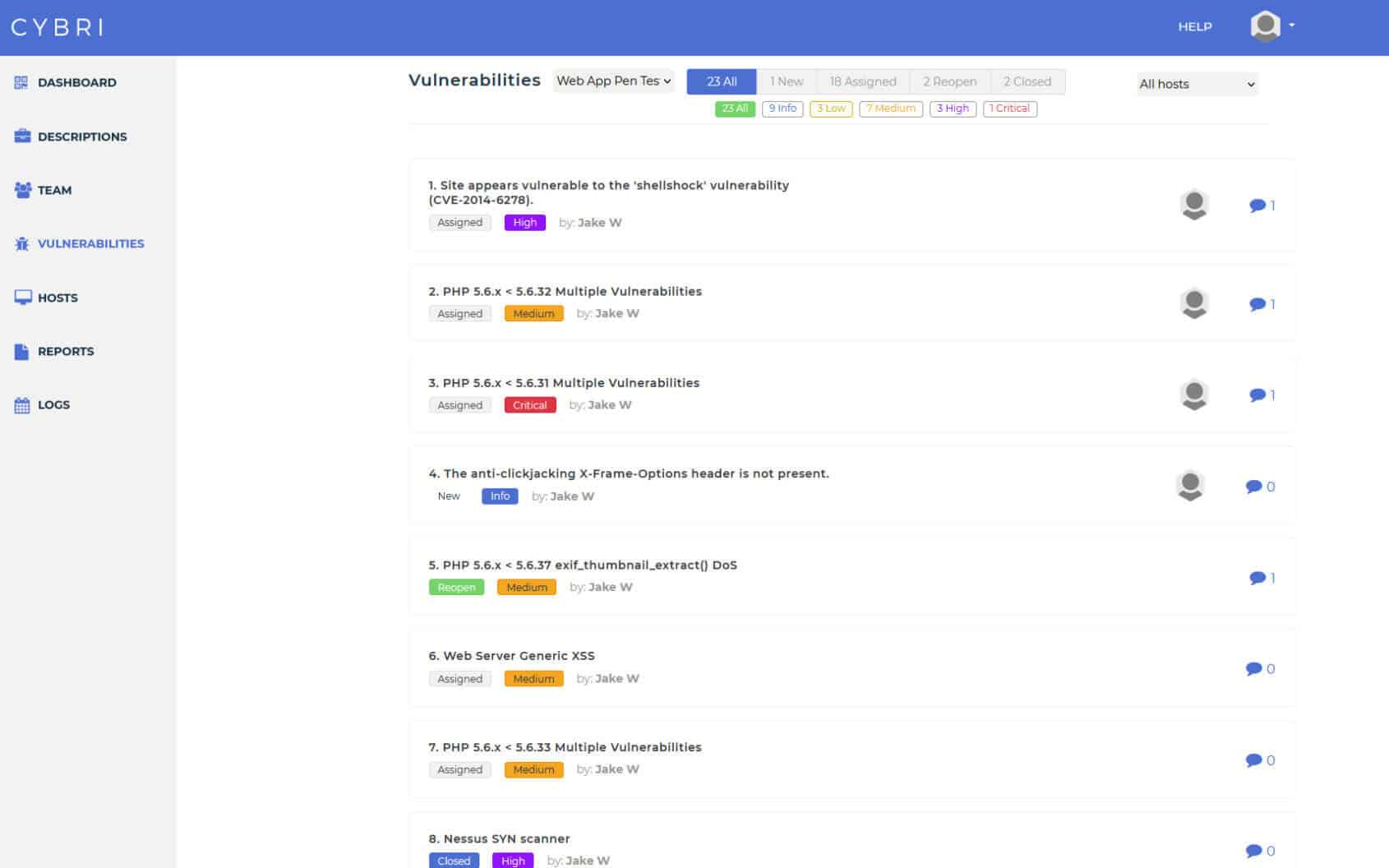
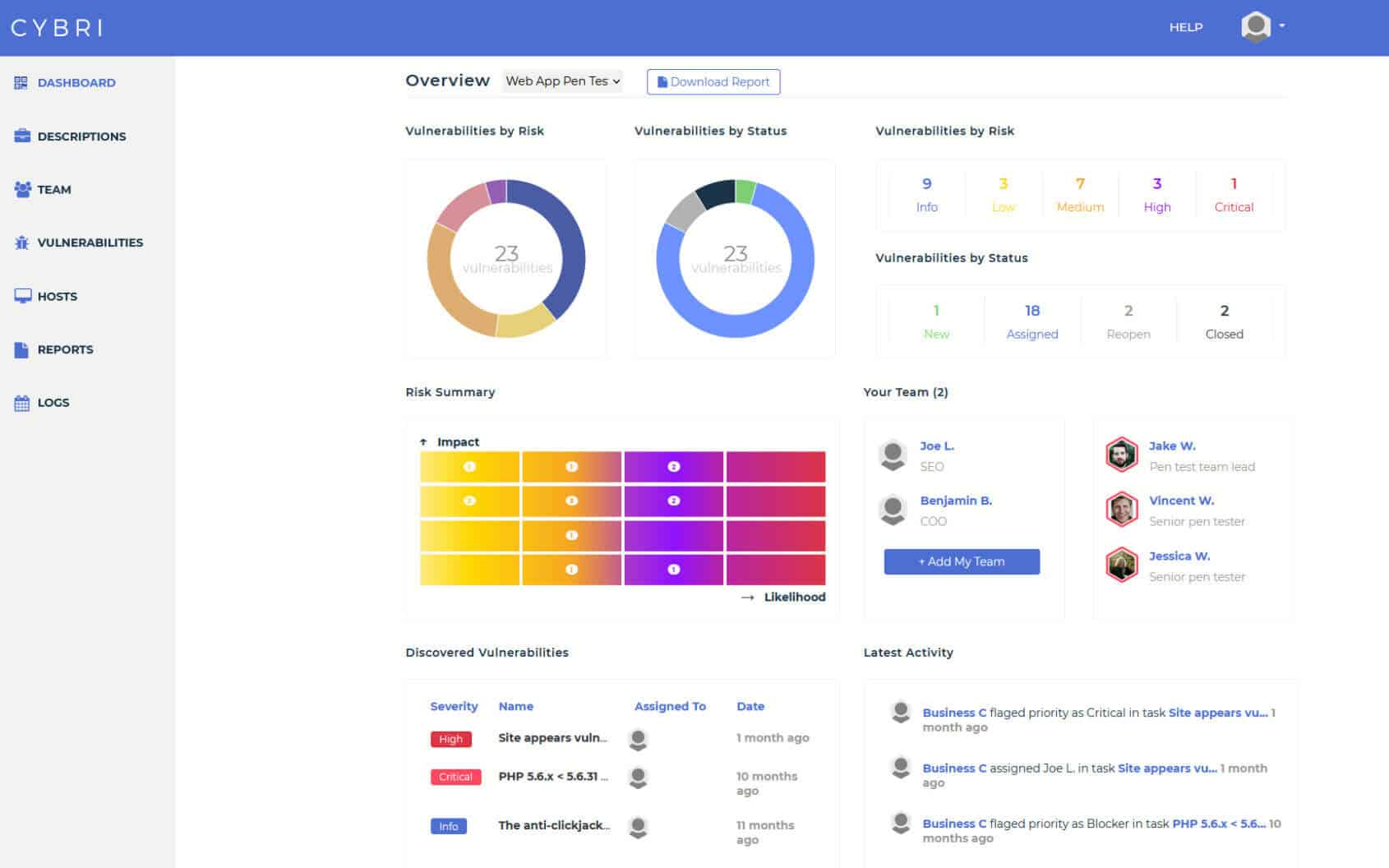
BlueBox Dashboard & Reporting
Easy access to clean and concise reports that can be shared among your executive and technical teams.
Transparent Process
We value visibility and transparency. Use our cloud-based platform to follow the pen testing progress and take action as our team detects new vulnerabilities.
What Our Customers Have to Say







What is manual testing?
How CYBRI Penetration Testing Works
Discovery
We will collect the needed information from you and your team to make sure that the right assets are being tested and the right team is assigned.
RED TEAM IN ACTION
CYBRI Red Team members will start testing your infrastructure and will ensure coverage of OWASP top 10 vulnerabilities. They will utilize their own techniques to ensure the highest levels and standards of testing.
Reporting
Collaboration
After each finding is verified by our Red Team members, they get submitted into your dashboard and report. Upon completion of each test, you will have a clear report that can be shared with executive and technical members as well as your clients.
Retest
Once the findings have been remediated by your team and the time is right to retest your technology, you can easily do so by scheduling a new test with us or by purchasing an annual package of multiple tests.
Repeat
Improve risk posture and decrease the liability of your organization. Asses the cybersecurity and risk of your organization on an annual engagement basis with the top five percent of the nation’s cybersecurity talent, the CYBRI Red Team.
We spend a week or more preparing before we execute. We will collect the needed information from you and your team to make sure that the right assets are being tested and the right team is assigned.
CYBRI Red Team members will start testing your infrastructure and will ensure coverage of OWASP top 10 vulnerabilities. They will utilize their own techniques to ensure the highest levels and standards of testing.
Communicate with CYBRI Red Team members about your vulnerabilities and assign the vulnerabilities for remediation to your team members; all directly in our platform. Our platform has a clear collaboration functionality to help your team with remediation of the findings.
After each finding is verified by our Red Team members, they get submitted into your dashboard and report. Upon completion of each test, you will have a clear report that can be shared with executive and technical members as well as your clients.
Once the findings have been remediated by your team and the time is right to retest your technology, you can easily do so by scheduling a new test with us or by purchasing an annual package of multiple tests.
Improve risk posture and decrease the liability of your organization. Asses the cybersecurity and risk of your organization on an annual engagement basis with the top five percent of the nation’s cybersecurity talent, the CYBRI Red Team.
What Sets Us Apart
What makes CYBRI one of the Premier penetration testing companies
Our outstanding penetration testing company services have attracted several clients that range from small startups to huge multinational companies. We are dedicated to improving cybersecurity across the board, which means that our services to your organization continue even after the pen test report has been delivered.
No matter the size of your organization, we will assess all of your cybersecurity needs from scratch to provide security measures tailored to your business needs. Our experts are always available to all of our clients in an advisory capacity should you wish to contact us.
What to Expect
- Initial pen tester meeting with CYBRI Red Team experts to determine the scope and develop a pen testing plan.
- Threat landscape mapping followed by active intelligence gathering to crack and identify any vulnerabilities, defaults, weaknesses, or misconfigurations.
- Transparency - regular updates and reporting about pen test findings via CYBRI Blue Box platform.
- In-depth findings report with images, descriptions, and vulnerability remedies.
Assessments
Schedule a personalized demo with CYBRI.
Don't wait, reputation damages & data breaches could be costly.








Discuss your Project