Vulnerability scanning is a security vulnerability test engagement against a computer system, network, or file server.
The type of security scan required for a particular system varies depending on what that system is intended to be used. The more complex and intricate the system or networks are, the deeper the security scans. You can perform a one-time scan of your system and network for malware, but most companies who implement this practice buy a service that continuously scans their systems and networks.
Since the beginning of computers, it has been around and can locate and exploit vulnerabilities in a computer network. There are also a variety of online scans available, but some are more effective than others, and some are more cost-efficient than others. A popular open-source software platform for scanning networks is called Nmap.
Types Of Security Scans
The most important thing to remember when deciding what kind of network and system security scanning a network and systems needs is always connected. It is essential to use a scanning method to examine every possible aspect of the computer network and system.
Therefore, a fully-featured security scanning solution needs to include a server security scanning feature. Network security issues can lead to servers being put at risk.
Network security scanning is essential because it helps to protect against cyber attacks. Networks lead to the computer systems used by companies, and if these networks are not adequately secured, then hackers and other threats can enter places where they shouldn’t be.
One of the biggest problems with network scanning is that they’re often incredibly complex. As the network grows, so too does its complexity.
Sometimes these additional layers contradict or take precedence over earlier ones, making things difficult. Network scans work by running vulnerability testing on network components.
The tests check any incorrect settings in the computers connected to the network, routers, and servers. The tests look for security issues, including misconfigured internet protocols (IPs), server settings, weak passwords, etc.
Once the scans have taken place, the risks can be assessed, allowing the network owner to make the right decisions.
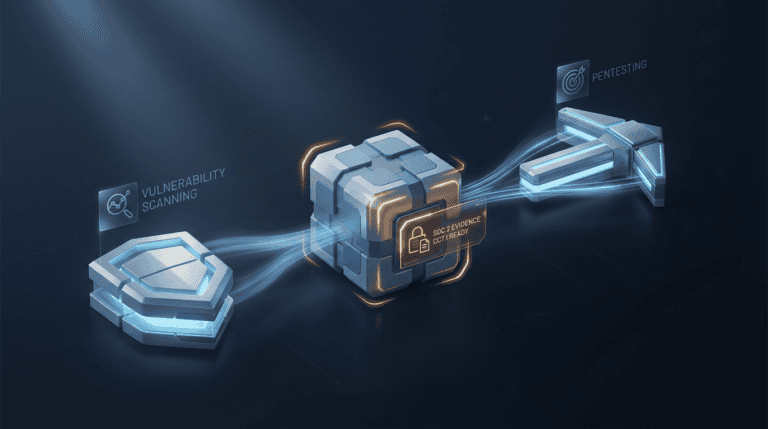
Vulnerability Scanning vs. Penetration Testing
Penetration testing exploits an architectural weakness in your system while vulnerability scanning checks for known vulnerabilities and reports on their risk exposure.
Penetration testing or vulnerability scanning depends on three factors:
- Scope
- Risk and Criticality of assets
- Cost and Time
CYBRI – Premier Penetration Testing Company
Headquartered in New York, CYBRI is a leading cybersecurity and penetration testing company in the US that protects from cyber threats for your organization.
Security hacks and cyber-attacks are evolving every day. You need to stay vigilant as there are many types of attacks and many ways to exploit even the most minor vulnerabilities your system may have.
Our excellent testing experts leave no stone unturned and will thoroughly test your applications, networks, and APIs for any security issues that may fall prey to any cyber-attack. We will identify the core problem and give you a detailed investigation report.
CYBRI Red Team (CRT)
We are backed up by Cybri Red Team (CRT) to help you achieve military-grade protection. Cybri Red Team is the best ethical hacker. They can dig out deep-rooted vulnerabilities in your web apps, cloud apps, mobile apps, network penetration testing, servers, IoT devices vulnerability assessment, etc.
CRT members are all US-based and are leading experts with the most recognized certifications, such as OSCP, GIAC, CISSP, and CEH. Some even carry experience from the US government, military, and Fortune companies.
Our penetration testing firm delivers elite penetration testing services and solutions to help our customers become more protected in the ever-growing cyber threat world. We help identify and remediate mission-critical vulnerabilities that might otherwise cost your company millions of dollars if exposed by hackers.
What makes CYBRI one of the Premier penetration testing companies?
Our outstanding penetration testing company services have attracted several clients that range from small startups to huge multinational companies. We are dedicated to improving cybersecurity across the board, which means that our services to your organization continue even after the pen test report has been delivered.
No matter the size of your organization, we will assess all of your cybersecurity needs from scratch to provide security measures tailored to your business needs. Our experts are always available to all of our clients in an advisory capacity should you wish to contact us.
Discuss your project with us!
Click here to go to our site, fill out the form, and the engagement team will contact you shortly!