Web App & API Penetration Testing Experts
Identify and Fix Security Risks in Web Apps, SaaS Platforms, and APIs.

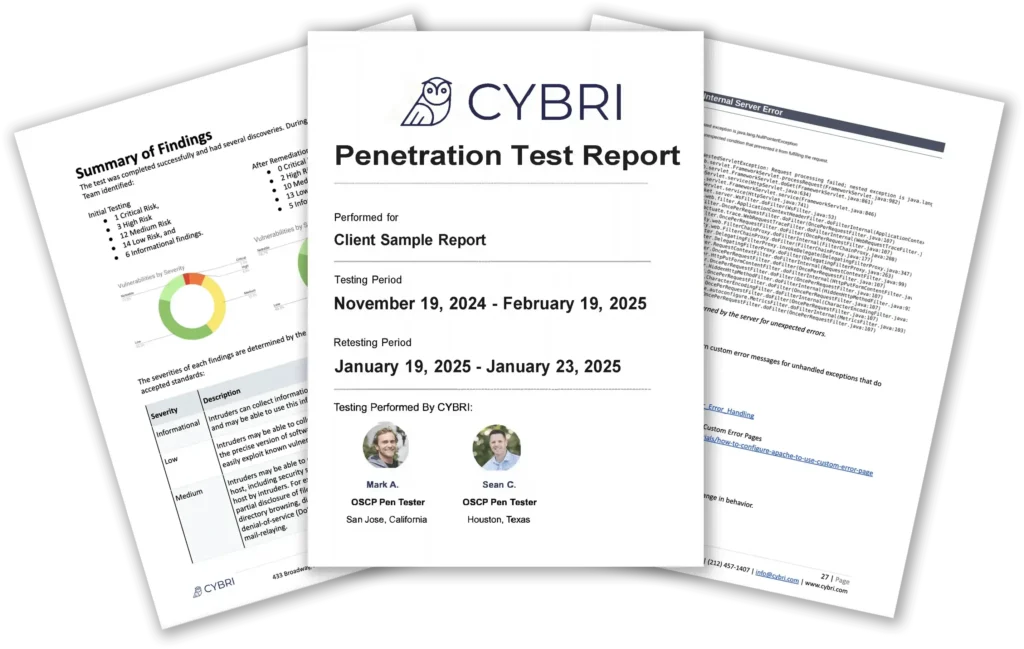
Certified Experts
Pen tests are conducted by OSWE, OSCP, and CEH-certified professionals for the highest accuracy and ethics.
Transparent Process
Get clear, actionable reports with evidence, remediation steps, and a dashboard for real-time tracking.

Complimentary Retest
We explain every finding in detail and offer a complimentary retest to ensure successful remediation.

8+ Years of Experience
Helping organizations strengthen security with expert penetration testing for over eight years.
8 Years Focused on Web App Testing
At CYBRI, we specialize in manual penetration testing for modern web applications, APIs, and SaaS platforms. Our team of OSCP, OSWE, and CEH-certified security professionals has been securing applications for over eight years, working with React, Angular, Vue, Node.js, Django, and other leading frameworks used by today’s tech companies.


Types of Penetration Testing We Offer
Web Application Penetration Testing
Identify and exploit vulnerabilities in your web applications, including authentication flaws, injection attacks (SQLi, XSS), and misconfigurations, ensuring your web app is secure against real-world threats.
Mobile Application Penetration Testing
Assess mobile apps for security risks, including insecure data storage, API vulnerabilities, reverse engineering threats, and improper platform permissions on iOS and Android.
API Penetration Testing
Test REST and SOAP APIs for authentication weaknesses, broken access controls, insecure endpoints, and injection vulnerabilities to protect critical data exchanges.
External & Internal Network Penetration Testing
Simulate real-world attacks to uncover misconfigurations, outdated software, privilege escalation paths, and lateral movement risks inside and outside your network.
Compliance Penetration Testing (HIPAA, PCI, SOC-2)
Ensure compliance with industry security standards by identifying risks related to data privacy, encryption, access controls, and regulatory requirements.
Cloud Penetration Testing
Evaluate cloud environments (AWS, Azure, GCP) for misconfigurations, weak IAM policies, exposed storage buckets, and other security risks unique to cloud infrastructures.
What Our Customers Have to Say







What Sets Us Apart
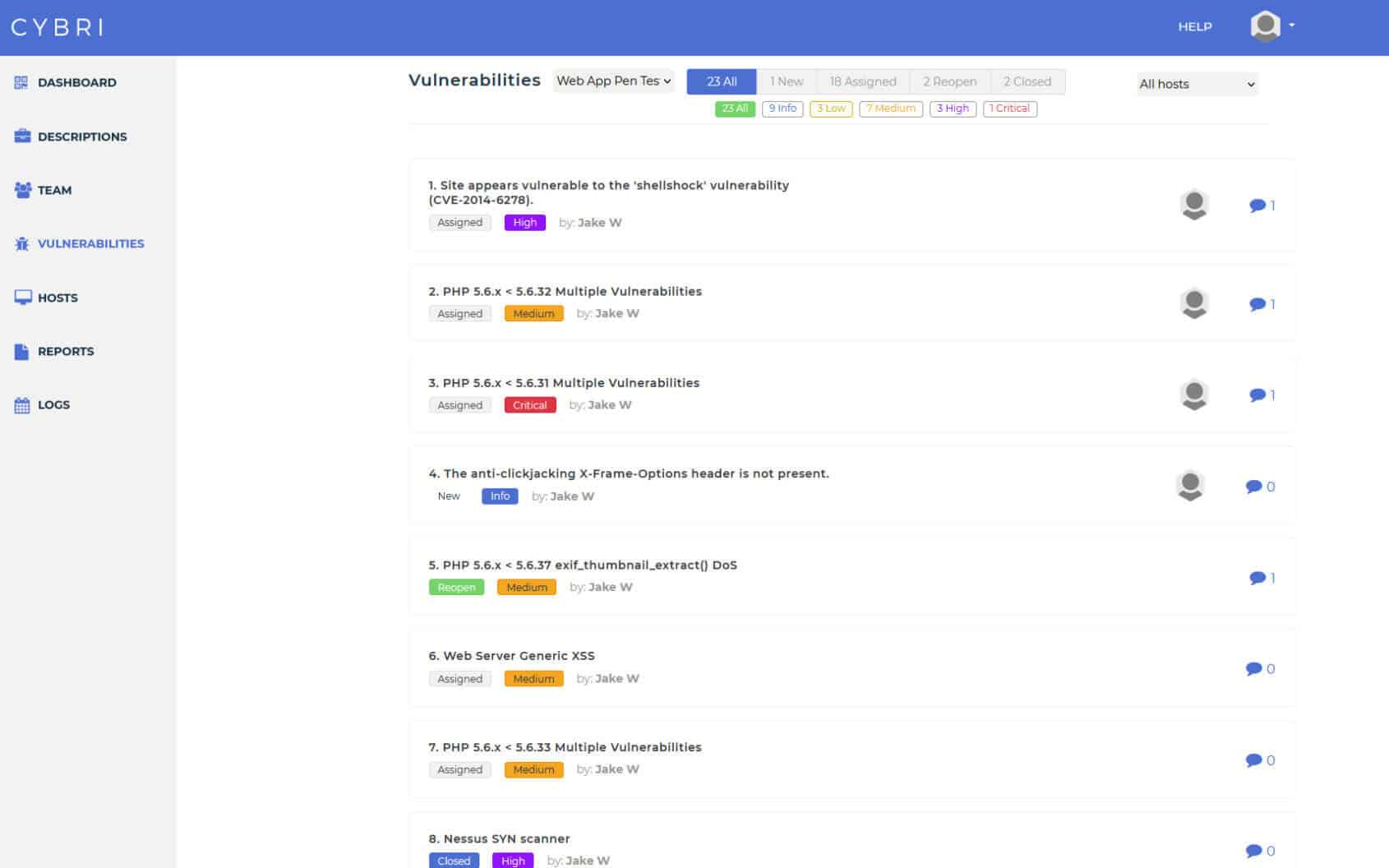
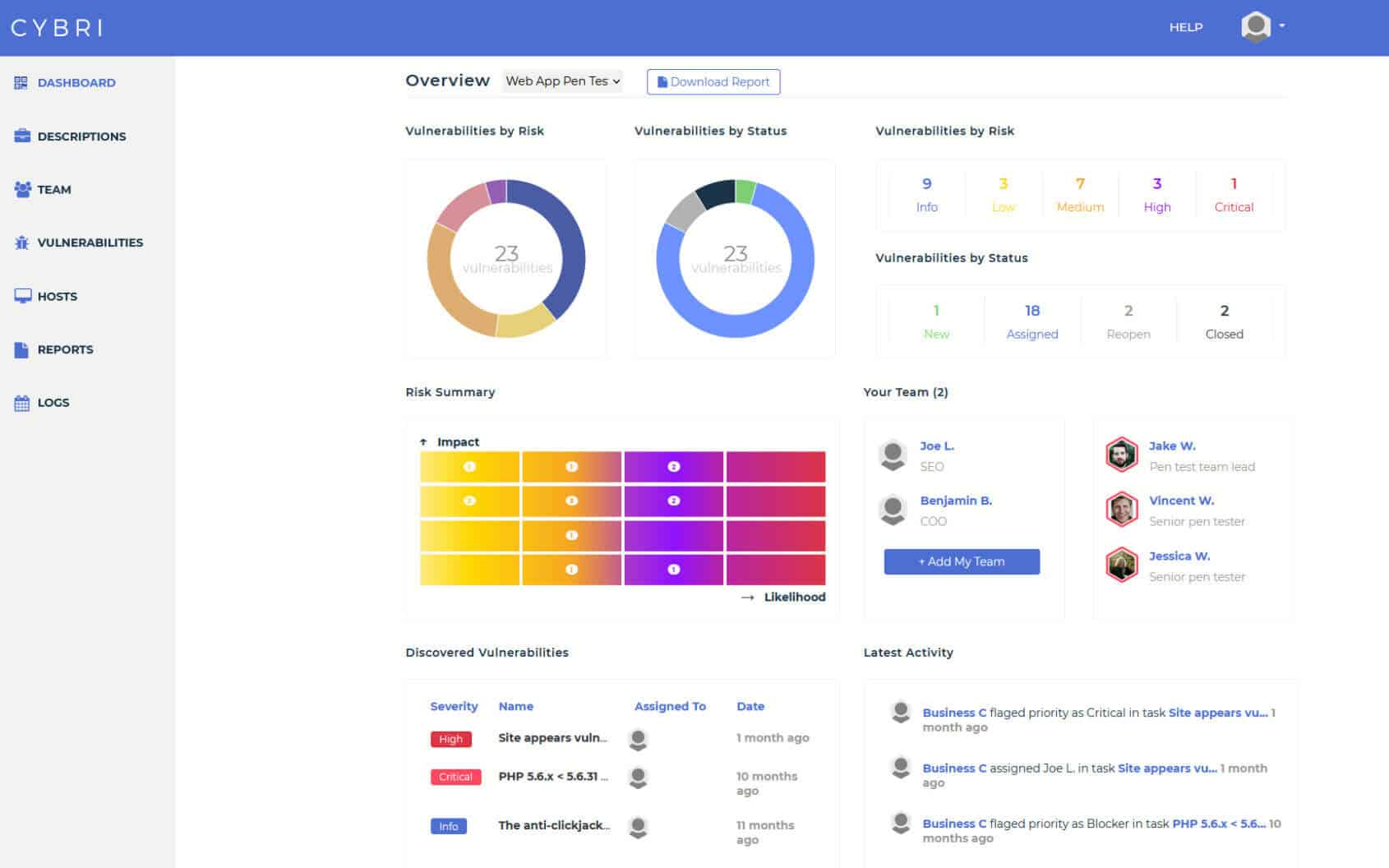
Use our proprietary BlueBox platform to collaborate with CYBRI’s highly qualified US-based penetration testers to detect critical vulnerabilities, sensitive data leaks, increase remediation, and access pen test results as they are discovered.
How CYBRI Application Penetration Testing Works
CYBRI web application penetration testing processes are on-demand hacker-powered penetration tests performed by one or two Red Team members. You pay a fixed price for your test and we do the rest. You can always increase the frequency.
Discovery
We begin by gathering information about your application, including its architecture, authentication mechanisms, and user roles. This phase helps define the scope and ensures a tailored testing approach.
PENETRATION TEST
IN ACTION
Our security experts simulate real-world attacks to identify vulnerabilities. Using manual and automated testing techniques, we assess your application’s security posture, focusing on areas like authentication flaws, data exposure, and access control issues.
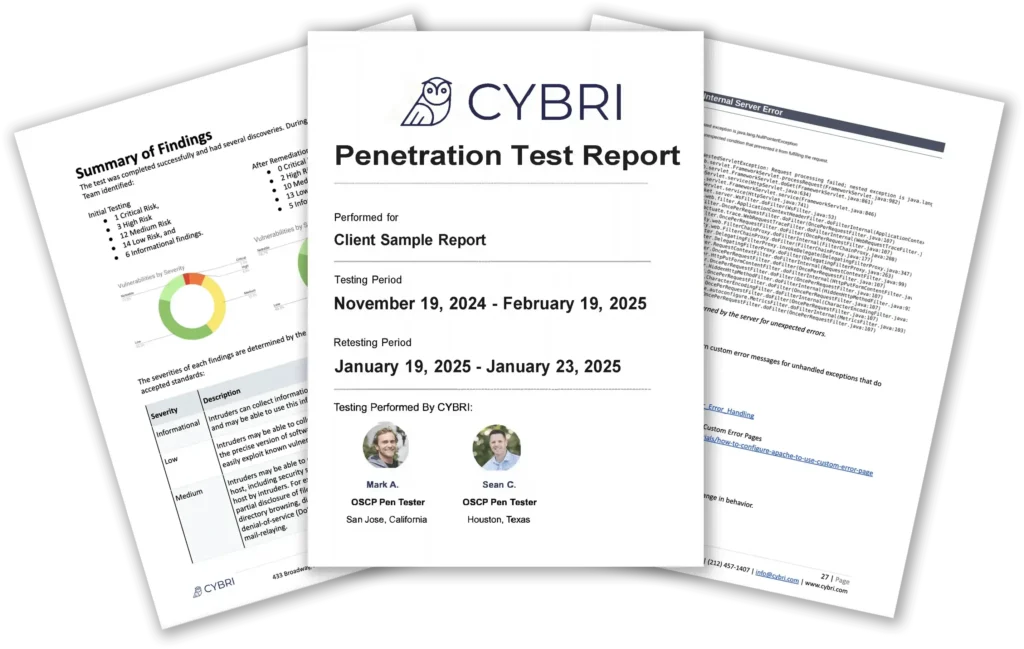
Reporting
You receive a detailed report outlining all discovered vulnerabilities, their risk levels, and clear remediation recommendations. The report is structured for both technical teams and executives to easily understand and act upon.
Collaboration
We walk you through the findings and answer any questions you may have. Our team provides additional insights into the risks identified, helping you prioritize remediation efforts effectively.
Retest
After you’ve addressed the vulnerabilities, we conduct a complimentary retest to verify that the fixes are effective, ensuring your application is secure against the previously identified threats.
We begin by gathering information about your application, including its architecture, authentication mechanisms, and user roles. This phase helps define the scope and ensures a tailored testing approach.
Our security experts simulate real-world attacks to identify vulnerabilities. Using manual and automated testing techniques, we assess your application’s security posture, focusing on areas like authentication flaws, data exposure, and access control issues.
You receive a detailed report outlining all discovered vulnerabilities, their risk levels, and clear remediation recommendations. The report is structured for both technical teams and executives to easily understand and act upon.
We walk you through the findings and answer any questions you may have. Our team provides additional insights into the risks identified, helping you prioritize remediation efforts effectively.
After you’ve addressed the vulnerabilities, we conduct a complimentary retest to verify that the fixes are effective, ensuring your application is secure against the previously identified threats.
Penetration Testing for Tech Companies
CYBRI specializes in web application penetration testing, using OWASP methodology to identify vulnerabilities and help tech companies meet SOC 2 and other compliance requirements.
✔ Front-End Security – XSS, DOM-based vulnerabilities, client-side injection flaws.
✔ Back-End API Security – Authentication misconfigurations, token hijacking, API abuse prevention.
✔ Authentication & Access Control – Role-based access testing, OAuth/SSO security validation.
✔ Business Logic & Data Protection – Preventing abuse of application workflows, securing data at rest and in transit.
FAQ – Web Application Penetration Testing
An application penetration test evaluates the security of your web, mobile, or API applications by identifying vulnerabilities such as authentication flaws, injection attacks, misconfigurations, and access control weaknesses. Our tests follow industry-standard methodologies, including OWASP Top 10 and NIST guidelines, to ensure comprehensive risk assessment.
The duration of a penetration test depends on the application’s size and complexity. Most tests take between one to three weeks, including the testing phase and report generation. For larger applications or those with complex integrations, additional time may be required.
Pricing starts at $5,000. Contact us for a tailored estimate.
To begin testing, we need a general understanding of your application, including how it’s built, how users access it, and its key functionalities. If available, documentation on system architecture, authentication methods, API endpoints, and user roles will help ensure a thorough and efficient test.
Yes, regular testing is highly recommended, especially for applications that frequently release updates. Many organizations perform tests quarterly or after significant code changes to ensure ongoing security.
Vulnerability scanning is an automated process that identifies potential security weaknesses, while penetration testing is a manual, in-depth assessment performed by security experts to actively exploit vulnerabilities and assess their real-world impact.
No, penetration tests are designed to be safe and minimally disruptive. We coordinate testing schedules and follow best practices to prevent downtime. If needed, we can conduct tests in a staging environment to avoid any impact on production systems.
After testing, you’ll receive a detailed report outlining vulnerabilities, risk levels, and recommended remediation steps. We also offer a complimentary retest to verify that the issues have been resolved and ensure your application remains secure.
While penetration testing is not a strict requirement for SOC-2 or HIPAA, it is commonly used to verify the effectiveness of security controls and identify vulnerabilities that could impact compliance. Our penetration tests help assess risks related to data protection, access controls, and system security, providing valuable insights for organizations preparing for compliance audits.
Let's Discuss Your Web App Penetration Testing Requirements
We specialize in web, API, and cloud penetration testing to identify vulnerabilities before attackers exploit them.
Provide a few details, and we’ll take care of the scheduling.







Discuss Your Project