Google Cloud Platform (GCP) has rapidly grown into a go-to cloud for modern businesses, from SaaS startups to large fintech and healthtech companies. But as cloud adoption soars, so do the stakes for security.
Recent industry reports reveal that “cloud security incidents are now more common than on-premises breaches” [1], and “more than 45% of all data leaks are due to cloud projects being breached” [2]. Misconfigurations and human errors are behind the vast majority of these failures, with “Gartner estimating around 99% of cloud security failures through 2025 will be the customers’ fault due to misconfigurations” [3]. For engineering and security leaders, this means proactively testing cloud environments is mission-critical to protect data and maintain trust.
This guide offers an executive-level overview of GCP penetration testing, covering what it is, why it matters, and how to approach it. Let’s dive in.
What Is GCP Penetration Testing?
In simple terms, GCP penetration testing is an authorized, ethical hacking exercise targeting a Google Cloud environment to identify and safely exploit vulnerabilities before malicious actors do. It involves simulating real cyberattacks on your cloud assets, such as your GCP-hosted applications, virtual machines, storage buckets, databases, APIs, and more, in order to find security weaknesses in configurations or code.
Compared to other types of pentests, a GCP test focuses on the customer-managed layers, meaning your cloud instances, configurations, applications, and IAM settings, rather than the cloud infrastructure itself. In contrast, a traditional on-prem test might include attacking the physical network or servers, which isn’t applicable in a fully managed cloud setting. GCP also relies heavily on service accounts for resource access, which introduces potential attack paths if those accounts are overly permissive or not properly scoped.
What are the Rules of GCP Pentesting?
Before launching into any security testing on Google Cloud, it’s essential to understand Google’s policies and rules of engagement. The good news is that “Google Cloud allows customers to penetration test their own GCP environments without prior approval, with a few important conditions” [4].
It’s worth noting that GCP’s stance here is a bit simpler than some other cloud providers. Amazon Web Services, for example, now also allows self-initiated pentesting on most of its services without approval, and Microsoft Azure similarly permits testing your own Azure instances as long as you follow their Cloud Acceptable Use Policy. Google’s approach is essentially: go ahead and test your cloud, just don’t violate our platform rules or harm others.
What Gets Tested in a Typical GCP Pentest?
A GCP penetration test will typically cover a broad range of cloud-based assets. Essentially, wherever your applications or data live in Google Cloud, a pentester will want to poke and probe those components. This includes virtual machines running on Google Compute Engine (GCE) and containerized workloads in Google Kubernetes Engine (GKE), as they are prime targets.
Cloud storage buckets (Google Cloud Storage) often contain sensitive data, so a pentest checks if any buckets are publicly accessible or permissively shared. Another common area to check is Identity and Access Management (IAM) services, as they govern who can do what in your cloud environment. Pentesters will scrutinize your IAM roles, service accounts, and policies to find privilege misconfigurations.
If you have applications running on GCP, they are tested much like any web or mobile app would be. The pentester will look for OWASP Top 10 style vulnerabilities such as SQL injection, XSS or broken access controls in your app code. Additionally, they will test API endpoints, as they are a relatively common entry point for attackers. Google Cloud’s networking services, such as VPCs, firewall rules and load balancers also require some attention, as well as port scans and network enumeration to identify open ingress points into your cloud environment.
Depending on the specific GCP configuration, the testers could also seek out weaknesses in CI/CD pipelines, or examine other Google Cloud Services in relation to your existing stack (think BigQuery, Pub/Sub or Cloud Functions, for instance). Essentially, any cloud service that houses critical data or connects to your application can be in scope.
Common GCP Security Weaknesses and Threats
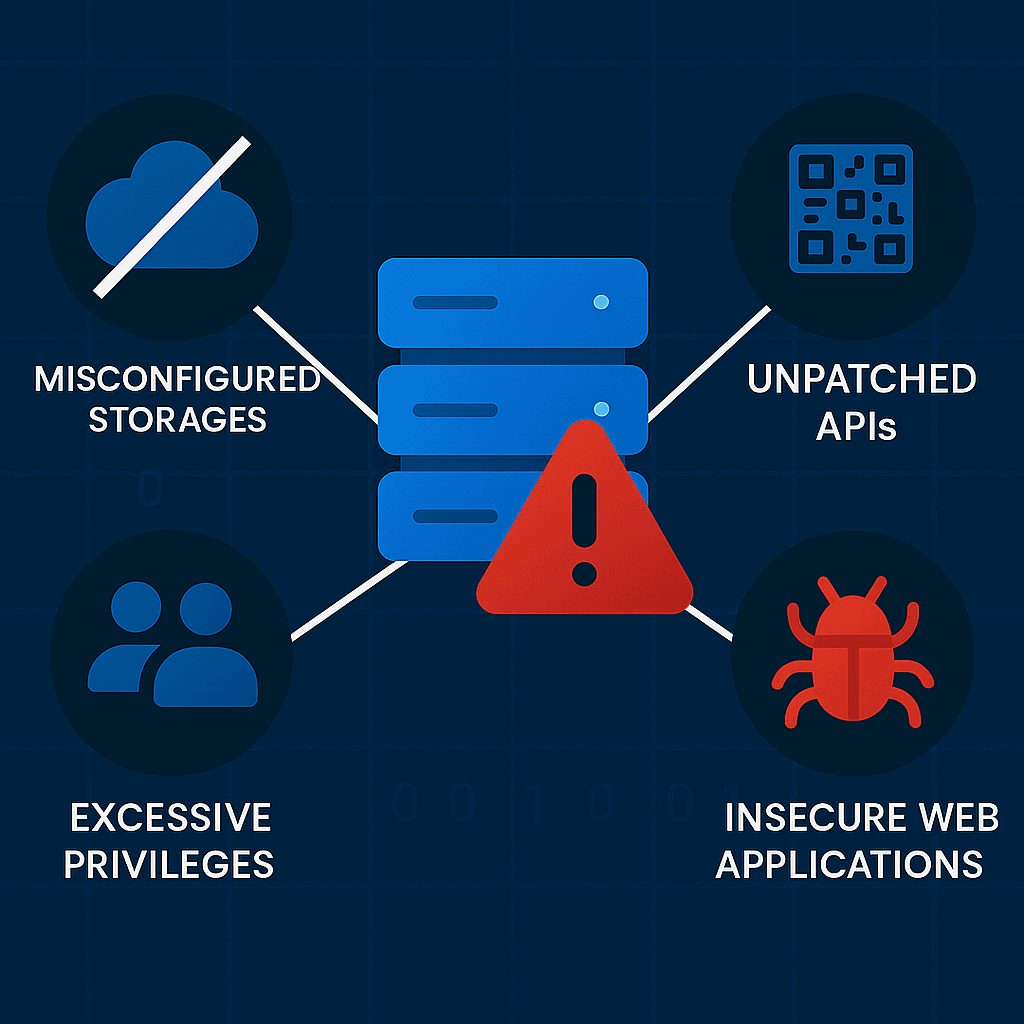
Even with Google Cloud’s robust platform security, there are several recurring weaknesses on the customer side that pentesters and attackers alike frequently encounter. For example, a misconfigured IAM role or policy can lead to full admin rights, which can easily result in severe data breaches if not caught in time. Similarly, storage buckets that are left open to the public internet can also lead to serious data exposure events, as sensitive files in an open bucket can be discovered by anyone. Therefore, pentesters should almost always check your IAM roles, storage buckets and overall cloud permissions, as this is one of the first things attackers do too.
Other weaknesses include weak network segmentation or firewall rules, as cloud networks should be treated with the same rigor as on-prem networks. Unfortunately, companies sometimes deploy GCP projects with default or flat network settings, which generally allows anyone on the internet to reach certain ports, exposing services such as databases, Redis caches, or admin panels that were never meant to be public.
A lack of robust logging and monitoring is more of a weakness in detection and response than initial vulnerability, but it’s still worth noting. Many companies fail to enable Cloud Audit Logs, VPC Flow Logs, or other monitoring in GCP. As a result, suspicious activities go unnoticed. In the context of pentesting, testers will check if their activities are being logged and alerted. If a tester can exfiltrate data or create new resources without anyone noticing in your ops center, that indicates that real attackers could do the same and dwell undetected.
Other weaknesses include unsecured APIs and endpoints that do not require authorization, allowing attackers to access sensitive information or inject vulnerabilities in the API parameters freely. Another common cloud weakness is when DevOps pipelines or automation scripts inadvertently expose secrets. Modern pentests increasingly include reviewing API endpoints as well as infrastructure-as-code and CI settings to scan for these potential issues.
How Is GCP Penetration Testing Performed?
Now that we’ve covered the general idea behind a GCP pentest, you might be wondering “how does a GCP pentest actually work in practice?” The process is similar to a standard penetration test but adapted to cloud scope, and it typically involves several phases carried out in a structured engagement. Let us examine the methods at a high-level.

Planning & Scoping
Every successful pentest starts with careful planning. The testing team will contact or meet with you to define the scope, such as which GCP projects, applications, and IP addresses are in bounds, and what’s out of scope. In this phase, roles and communication channels are established to ensure everyone agrees on the objectives and boundaries to avoid surprises.
Reconnaissance & Enumeration
The pentesters then move into the information-gathering phase. They’ll enumerate your GCP footprint using both passive and active recon. This might include mapping out your external footprint, such as DNS records, subdomains etc. They typically also gather public information if possible, such as leaked credentials in public repos or employees to target with social engineering. The idea is to develop a comprehensive list of possible entry points, much like an attacker would in the early stages.
Vulnerability Discovery
Next, the testers use automated tools and manual techniques to find weaknesses. Automated cloud configuration scanners are commonly used to assess your GCP configurations against security best practices. Similarly, testers might use tools to enumerate storage buckets and test their accessibility, or custom scripts to list IAM roles looking for policy issues. They will also scan web apps with vulnerability scanners, run network port scans on discovered IPs, and so on. This phase often uncovers a laundry list of potential issues, which the team prioritizes for exploitation.
Exploitation & Attack Simulation
This is where the pentesters begin their actual attacks (within the agreed scope, of course). Their goal is to attempt exploiting the identified vulnerabilities to prove their impact. For example, if a database was found open, can they actually connect to it and extract data? In the cloud context, exploitation might also involve chaining issues. For instance, the tester might use stolen credentials (often obtained from a public Git repo or an open metadata service) to move laterally through your GCP project. They might impersonate a service account to access another service’s data. An ongoing pentest at this stage often provides daily updates during this phase, especially if something critical is breached. so you can take action if needed.
Reporting & Debrief
After the active testing window closes, the pentesters compile their findings into a detailed report. This report will typically list each vulnerability discovered, its severity/impact, the evidence showing how it was exploited, often mapping issues to relevant compliance or security frameworks to SOC 2 controls for instance. Once delivered, a debrief meeting is usually held where the pentesters walk through the findings with your team, ensuring you understand each issue and how to fix it.
Remediation & Retesting
The ultimate goal of a pentest is not the report itself, but the improvement of security. After the test, your engineering and DevOps teams will work to remediate the identified vulnerabilities, often by locking down bucket permissions, tightening IAM roles, patching VMs, implementing MFA, etc. Many penetration testing providers include a retesting phase (or offer it as an option), meaning that once you claim to have fixed an issue, the tester can come back and verify the fix.
Typical outcomes you can expect include a list of confirmed vulnerabilities (with evidence of what data or system access was gained), a set of recommendations ranked by priority, and often an overall score or risk rating of your cloud security posture.
Cybri: Your Go-to Partner for GCP Pentesting
As you consider tackling GCP penetration testing, to uncover vulnerabilities in configurations, IAM policies, storage buckets, APIs, and other services before malicious actors exploit them, having the right partner can make all the difference in getting actionable results. And the upside is alluring, as by proactively identifying and remediating risks, businesses can prevent data breaches and maintain compliance in an increasingly cloud-centric threat landscape.
Cybri’s GCP penetration testing services combine deep cloud expertise with hands-on ethical hacking to uncover critical risks like IAM misconfigurations, exposed storage, and exploitable vulnerabilities, validating each finding with real-world impact. Our team prioritizes actionable remediation, offering clear fixes and compliance mapping (SOC 2, HIPAA, PCI-DSS) while supporting retesting to confirm security gaps are closed.
Through our BlueBox platform, clients get real-time visibility and direct collaboration with US-based testers, ensuring transparency and adaptability for dynamic cloud environments. With experience across fintech, healthcare, and SaaS, we deliver tailored assessments that align with both technical and regulatory needs.
Frequently Asked Questions
GCP environments are powerful but complex, often spanning numerous services like Compute Engine, Cloud Storage, IAM, and Kubernetes. That complexity introduces risks, from misconfigured IAM roles, to open storage buckets, excessive permissions, exposed APIs, and more. Penetration testing simulates real-world attack techniques to expose these gaps before threat actors can exploit them. For security teams operating in a fast-moving DevSecOps environment, regular GCP pentesting is one of the most effective ways to validate cloud security posture and catch critical issues.
At minimum, you should conduct a penetration test annually, or after major changes to your GCP environment. Key trigger events include launching a new application, migrating to new GCP services, significant architecture changes, or introducing sensitive data workflows. If you’re working toward a compliance goal (like SOC 2 or HIPAA), pentests should be scheduled in sync with audit timelines.
No. Prior approval is not required for most penetration tests on GCP resources that you own. Google Cloud explicitly allows customers to test their own environments as long as they follow the Acceptable Use Policy. This means sticking to your project boundaries, avoiding DoS-style testing, and not attempting to access other customers’ data or core Google services.
It varies. Depending on the scope and methods used, penetration testing can temporarily affect GCP performance and may generate additional costs. For example, brute-force tests against APIs or large-scale enumeration of buckets and services may result in elevated usage charges. That’s why experienced pentesters plan engagements carefully: defining safe test windows, using throttling, excluding production traffic flows, and choosing testing zones with cost awareness in mind.
Yes. While frameworks like SOC 2, PCI DSS, and HIPAA don’t always require penetration testing explicitly, it’s often expected as evidence of due diligence. For example, SOC 2 auditors look for how your organization identifies and remediates security vulnerabilities, and regular pentesting checks that box. PCI DSS requires external testing for cardholder data environments, and HIPAA expects covered entities to assess technical safeguards.










