Why This Guide Matters
GDPR is technology-neutral; it does not mandate specific tools but obliges data controllers and processors to ensure data security and “regular testing, assessing, evaluating” of measures.
Penetration testing is a well-established method to demonstrate that technical and organizational measures (TOMs) are effective in practice.
For SaaS vendors handling EU user data, a GDPR-aligned pentest helps support reporting, DPIAs, vendor-risk reviews, and demonstrates “security-by-design” and “security-by-default.”
GDPR Context & Relevant Articles
| Article | Context |
| Article 32 (Security of Processing) | implement appropriate security, test regularly. |
| Article 25 (Data Protection by Design and by Default) | validates that implemented privacy/design controls work as intended. |
| Article 30 (Records of Processing Activities) | pentest scope should map to declared processing activities. |
| Article 35 (DPIA for High-Risk Processing) | findings feed into risk/impact assessment. |
What Is GDPR Penetration Testing?
At its core, penetration testing (or “pen testing”) is an authorized, controlled attempt to evaluate the security of your systems by simulating real-world attacks. Think of it as hiring a skilled locksmith to examine your building not only checking whether the doors are closed, but testing whether the hinges, frames, alarms, and access rules work the way you believe they do.
So, how does this apply to GDPR?
GDPR does not mandate penetration testing by name. Instead, it requires organizations to implement “appropriate technical and organisational measures” to protect personal data, and to have a process for “regularly testing, assessing, and evaluating” those measures (Article 32(1)(d)).
A GDPR-aligned penetration test is therefore not a generic security exercise.
It is a targeted evaluation focused on systems and processes that store or handle personal data, designed to check whether the safeguards you’ve put in place actually work in practice.
Your organization makes specific statements in DPIAs, privacy notices, and internal documentation – for example:
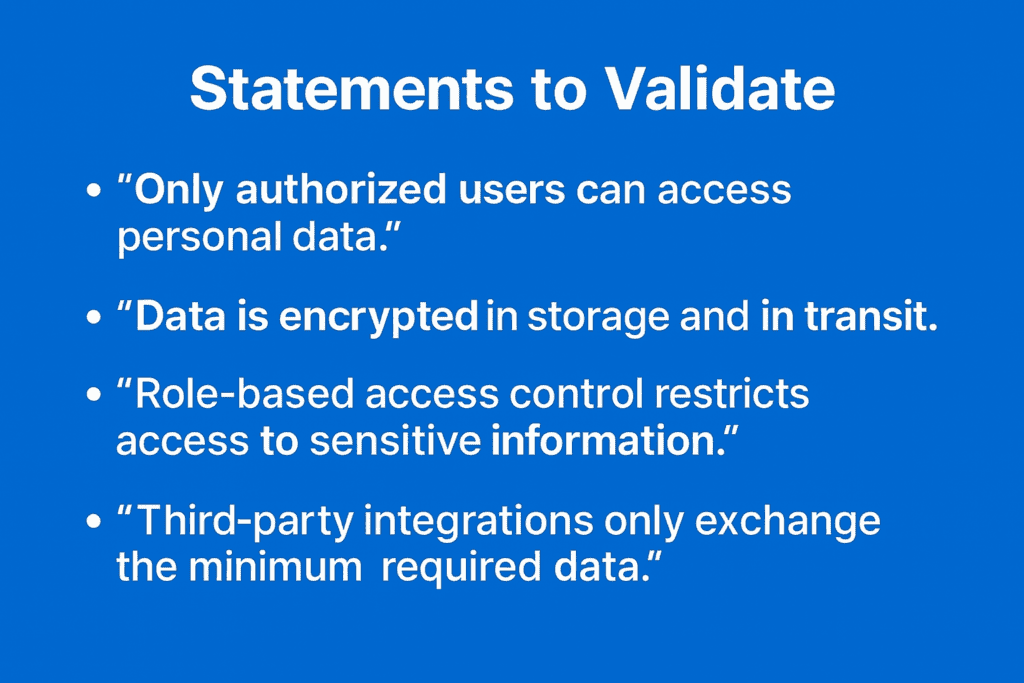
A GDPR penetration test is where you validate those claims with evidence.
Our job as testers is to challenge these assumptions directly.
If you state that only certain roles can view customer information, we will walk through that path, test boundaries, and see whether privilege checks behave as intended. If you say data is encrypted, we verify how and where. If you note that only specific APIs receive personal data, we trace data flows and try to violate those boundaries.
The results give your legal team, and security leadership objective, third-party evidence showing one of two things:
- Your technical measures are effective, and your GDPR documentation is accurate;
- or there are gaps – where controls do not behave as expected, personal data could be exposed, or additional risk-reduction measures are required.
A GDPR penetration test therefore supports the regulation’s core expectations:
privacy by design, risk management, accountability, and the ability to demonstrate that security measures truly work in practice.
Is Penetration Testing Required for GDPR Compliance?
No – GDPR does not legally require penetration testing.
The GDPR is technology-neutral and avoids naming specific tools or certifications. You will not find the words penetration test, vulnerability scanning, or security audit anywhere in the regulation.
Instead, GDPR sets risk-based obligations through broad requirements:
- Article 32(1): “Appropriate technical and organisational measures”
Organizations must protect personal data using safeguards appropriate to:
- the risks
- the nature of processing
- the impact on individuals
- Article 32(1)(d): “Regularly testing, assessing, and evaluating”
This is the closest GDPR gets to technical testing.
It requires a process, not a specific activity.
GDPR therefore leaves open how an organization fulfills that obligation.
Why Penetration Testing is Commonly Used, but Not Mandatory
Although GDPR does not require a pentest by name, many organizations choose it because:
1. It is one acceptable method to satisfy Article 32(1)(d).
Penetration testing provides structured evidence that technical controls (authentication, access control, encryption, segregation, etc.) are functioning as described.
GDPR expects effectiveness, not just policy documents.
2. DPIAs (Article 35) often need real evidence, not assumptions.
A Data Protection Impact Assessment must evaluate:
- likelihood and severity of risks
- mitigations and their effectiveness
Pentest findings can support this evaluation, especially for high-risk processing.
3. Supervisory authorities and regulators mention pentesting as a recommended measure.
Regulators (such as the UK ICO and EU Working Party/EDPB in guidance) frequently list pentesting as an example of:
- good practice for detecting vulnerabilities
- a valid way to satisfy “regular testing” obligations
They do not say it is mandatory.
When to Perform a GDPR Penetration Test
- Before or after major changes in data processing systems (new features, cloud migration, new subprocessors).
- Periodically – e.g. annually or bi-annually – especially for high-risk or high-volume processing.
- After integrating third-party services, or when adding new data flows or sensitive data types.
- Before major roll-outs to EU customers, or prior to vendor-risk audits / procurement reviews.
What a GDPR Pentest Should Cover
Deliverables & Report Structure

A GDPR-aligned pentest report should include:
- Executive summary / compliance summary
- Scope & methodology (what was tested, how, disclaimers)
- Findings with impact explanation – not only CVSS, but what data was affected, what risk to data-subjects, what business functions
- Mapping of findings to GDPR obligations (Article 32, 25, etc.) and recommended security-by-design / default controls or mitigations
- Data flow diagrams (before & after remediation where possible)
- Remediation guidance and prioritized risk/impact matrix
- Retest results if remediation was applied, demonstrating continuous control effectiveness
- Documentation suitable for DPIA updates, vendor-risk forms, compliance evidence
| Process | Engagement Flow |
| Scoping & Data-Flow Mapping | define systems, data types, storage/processing flows, subprocessors. |
| Pre-test information gathering | architecture, config, access controls, encryption, laws/data-subject scope. |
| Penetration Testing Execution | manual testing across agreed assets (app, API, infra, cloud) with privacy-safe methodology (minimised data exposure, pseudonymisation where possible). |
| Report & Risk Assessment | results with GDPR-specific context (data-subject risk, breach potential, regulatory impact). |
| Remediation & Retesting | verify fixes. |
| Compliance Evidence Delivery | ready for auditors, vendor-risk assessments, DPIA, internal governance |
Why Pentesting Adds Value Under GDPR (Compared to Passive or Automated Measures Only)
- Demonstrates real-world control effectiveness – not just theory or config.
- Validates business logic and data-handling behavior (not testable via scanning).
- Supports DPIA with empirical data.
- Provides objective proof for vendor-risk, audits, customer due diligence.
- Shows commitment to “state-of-the-art” security.
Limitations & When Pentesting May Not Be Enough
- Pentest is a point-in-time assessment real security requires continuous monitoring, secure dev practices, patching, and good operations.
- Sensitive data handling (live data) may require test data or pseudonymization.
- Pentest cannot prove 100% absence of risk and combines with other controls (logging, encryption, access control, processes).
- For some obligations (data retention, data subject rights, subprocessors’ compliance) technical pentest is only one part.
Complementary Measures (What to Combine with Pentesting for Full GDPR Posture)
- Vulnerability scanning and continuous VA (for new CVEs / config drift)
- Secure coding, code review, SAST/DAST / automated security testing
Conclusion & Recommendations
- A structured, GDPR-aligned penetration test offers one of the most credible, defensible, and actionable ways to meet that requirement especially for SaaS/data-processing providers.
- For maximum compliance readiness: combine pentesting with continuous security practices, documentation, and operational controls.
- Use the deliverables from this process as part of your compliance, DPIA, vendor-risk, and audit-ready documentation.
Need GDPR-Aligned Penetration Testing?
Cybri helps organizations perform GDPR-focused penetration testing across web applications, APIs, cloud environments (AWS, Azure, GCP), and on network infrastructure. We support SaaS platforms, startups, fintech, healthtech, and enterprise organizations in validating the effectiveness of their technical and organizational measures (TOMs) under GDPR.
Navigating GDPR’s security requirements, especially the obligation to “regularly test, assess, and evaluate” controls can be complex. Whether you are preparing for a DPIA, expanding into the EU market, or strengthening accountability and security-by-design, evidence-based security testing is essential.
Cybri’s GDPR-aligned penetration testing provides objective validation that your web applications, APIs, and underlying systems protect personal data effectively, helping you reduce risk, demonstrate compliance, and maintain trust with EU customers and regulators.
Talk to our team at Cybri about your GDPR compliance objectives, upcoming DPIAs, or EU expansion plans, and learn how we can help you achieve effective, evidence-based, and auditor-ready security assurance.
References
ICO – A guide to data security
ICO – Security outcomes
GDPR art 32 – Security of processing
GDPR art 35 – Data protection impact assessment
FAQs
Why do I require penetration testing for GDPR compliance?
No, but penetration testing provides concrete evidence that the technical and organizational measures required under GDPR Articles 5, 24, 25, and 32 actually work in practice proving that personal data is secured against real-world attacks, not just documented on paper.
What happens if we uncover high-risk findings during our GDPR pen test?
Critical and high-risk findings must be promptly remediated and retested, with documented evidence of resolution provided to your auditor.
Can internal teams perform pen testing for GDPR compliance?
Penetration testing that supports GDPR compliance must be performed by independent third-party experts; internal staff cannot provide the objective, credible validation required under GDPR.
Do I need a pen test to pass GDPR?
GDPR doesn’t explicitly require penetration testing, but you must demonstrate the effectiveness of your security measures—and penetration testing is the most credible way to do that.How often should we conduct penetration testing for GDPR?
Penetration testing for GDPR should happen at least once a year, after major changes, and whenever DPIAs or incidents indicate elevated risk, ensuring you can prove your controls remain effective under Article 32.














