Stolen medical data can fetch up to 50 times more value than financial data on the black market, making healthcare data a high-value target for cyber criminals [1]. Thanks to a rising tide of breaches, healthcare companies are facing extreme costs and strict compliance mandates like HIPAA. With the average data breach in healthcare costing over 10 million USD [2], penetration testing has become a critical defense measure for companies looking to avoid disruption and costly breaches.
If you’ve never conducted a penetration test, getting started may seem daunting. In this guide, we’ll walk you through the essentials, show you how to start a testing program. And cover why healthcare is vulnerable, what a test entails, and how to choose a partner to protect patient data and meet your security and compliance goals.
The Unique Security Challenges in Healthcare Environments

Third-Party and Vendor Risks
Cloud Adoption and Telehealth Expansion
Healthcare has widely adopted cloud services and telemedicine, particularly after the COVID-19 outbreak. The increase in telehealth usage was over 3000% across 2020 while COVID -19 was in full swing and virtual care is still far more than prior to 2020. While cloud-based EHRs, patient portals and telemedicine applications improve access, they bring new security threats. Information stored within cloud applications may not be secure sufficient, improperly configured, or vulnerable without sufficient network security.
Balancing Security with Patient Care
Lastly, healthcare IT systems are life-critical, meaning they absolutely have to be up at all times to enable patient care. This makes hospitals an attractive target for ransomware and denial-of-service attacks. Healthcare providers are unable, unlike other industries, to bring down system after system with prolonged maintenance or security patches, nor are they capable of withstanding downtime.
The attackers are aware of this squeeze, and given that over 57% of healthcare organizations have reported cyberattacks that impaired patient care. Penetration testers are also aware of such high stakes and design engagements with caution so that no disruption occurs.
The Top Cybersecurity Threats in Healthcare Today
Phishing
Phishing means attackers send spoof emails or messages pretending to be trusted sources. They aim to trick people into sharing credentials or downloading malware. In healthcare, a phishing email may pretend to come from IT and ask employees to reset VPN passwords on a fake portal. This lets attackers steal login credentials. Penetration testing can include simulated phishing as part of social engineering tests.
Information Breaches
Data breaches and ePHI theft in healthcare mean unauthorized access or theft of electronic protected health information (ePHI). Attackers may hack databases, steal data using malware, or act as insiders. Penetration testers think like attackers and search for the same weaknesses in your defenses. They probe external networks and web applications to find common breach vectors and help close security gaps.
DDoS Attacks
Ransomware encrypts files or systems and demands payment for a decryption key. DDoS attacks flood systems or websites with traffic, causing downtime. Pen testers use similar ransomware techniques to assess how far attackers could go and access critical systems. For DDoS, testers review mitigation measures and may run limited stress tests.
Obsolete technology
Legacy systems include outdated software and medical equipment that organizations still use due to compatibility needs or budget limits. These systems often lack modern security updates and contain vulnerabilities that newer technologies have already fixed. Penetration testers identify these weak points by actively exploiting known legacy vulnerabilities and providing practical recommendations to reduce risk without disrupting business operations.
Vulnerabilities in Medical Applications and Devices
Healthcare penetration testing finds critical vulnerabilities in apps like mobile health tools and telemedicine platforms before attackers exploit them. For example, patient portal flaws may allow unauthorized access to protected health information (PHI). Pen testing simulates real attacks, checking insecure APIs and broken authentication to protect patient data.
Assets that Commonly Get Tested in Healthcare
Internal and External Networks
Healthcare network tests often find open ports, outdated systems, weak domains, and poor segmentation. Hospital networks connect all systems, so one misconfiguration can cause a full breach.
Ransomware often starts from exposed services, so testing finds issues early. Pen testers perform external scans and simulate internal attacks after breach.
Web and Mobile Applications
Healthcare organizations have numerous applications, ranging from patient portals, scheduling, and telehealth video platforms, through mobile apps for tracking or messaging and so forth. Many applications handle sensitive patient data and must be accessible online, which significantly increases security risks.
Pen testing web and mobile apps can uncover vulnerabilities such as SQL injection, broken access controls, or inadequate encryption of data in transit. Testing apps ensures that this layer of your environment – the one directly used by patients and doctors – is secure against the most likely attacks.
Medical Devices and IoT
From MRI machines and infusion pumps to “smart” IV drips and patient wearables, the Internet of Medical Things (IoMT) is vast in a modern hospital. Pen testers can typically evaluate live medical devices in isolated instances, or verify new technology before it becomes widespread in the organisation.
This is important, since compromised medical devices can not only expose data but potentially threaten patient care. There have even been FDA alerts about device vulnerabilities. Regular penetration testing and risk assessment for IoMT helps identify those weaknesses so you can work with vendors to patch devices or put compensating controls in place
The Role of HIPAA Compliance in Healthcare
Penetration testing is widely regarded as an “addressable” measure under HIPAA. In other words, if it’s reasonable and appropriate for your organization, you should be doing it as part of meeting the requirement to “protect against reasonably anticipated threats” [5]. In fact, NIST (National Institute of Standards and Technology) offers guidance for HIPAA that specifically recommends penetration testing to validate the effectiveness of security controls.
Pen tests provide real-world evidence that you’ve reviewed your security and remediated vulnerabilities, exactly what the auditor requires. It’s far better to find and remediate weakness via a controlled pen test than have it turned against you via breach, which comes with investigations and non-compliance fines. But that’s above and beyond the damage from the breach itself.
How Your Organization Can Engage in Penetration Testing
Ready to start penetration tests at your healthcare organization? By following the guide’s instructions, the tests will be effective, safe, and aligned with your goals.
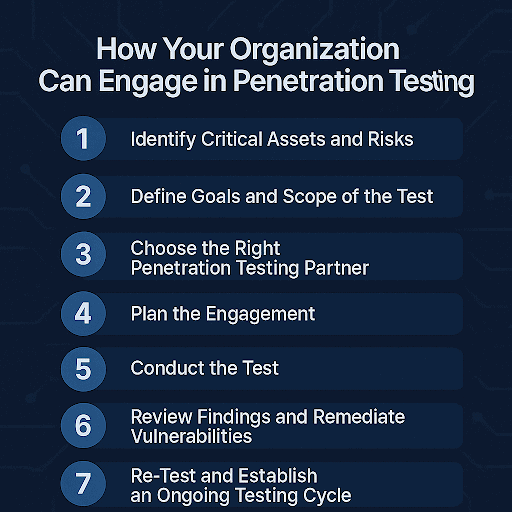
Step 1 Identify Critical Assets and Risks
First, identify your most critical protection needs. In healthcare, this usually relates to systems that store or operate on ePHI (an electronic form of protected health information), life-critical medical devices. Their core network infrastructure, and high-value web applications. Include participants from IT, security, compliance, and clinical divisions while creating an asset inventory.
Step 2: Define Goals and Scope of the Test
Next up, you should work on figuring out your requirements and overall goals. Are you trying to uncover as many vulnerabilities as possible across your entire network (broad assessment)? Or are you targeting a specific area, like a new patient mobile app or a recently deployed network segment (focused assessment)? A well-scoped test will concentrate on the highest-risk areas without accidentally disrupting sensitive operations.
Step 3: Choose the Right Penetration Testing Partner
Choose the right penetration testing partner if you don’t have qualified internal red teamers yourself. Remember that not all pen testing providers are equal, so look for one with healthcare experience, knowledge of compliance, and a methodology that fits your needs. Does your candidate have references in healthcare? What certifications do their testers hold? Will they provide a detailed report with remediation guidance?
Step 4: Plan the Engagement
When articulating plans and regulations, make certain that you coordinate with your chosen partner. Setting up tests at such a time that disruption of operations is held to the minimum, with all legal and contract documents signed and finalized. Schedule with your IT personnel so that they don’t mistake the activities of the tester with an attack, nor make unintended changes within the test time span.
Step 5: Conduct the Test
Now you’re ready to let the pen testers do their real job, according to the plan that’s been agreed. While they test, they’ll generally employ some combination of automated scanners and manual methodologies aimed at discovering and taking advantage of vulnerabilities. They may, for instance, perform port scans and vulnerability scans of your network, attempt SQL injection. Or probe default passwords of medical equipment.
Step 6: Review Findings and Remediate Vulnerabilities
Review findings and remediate vulnerabilities after testing, as the penetration testers will provide a detailed report of their findings that helps you determine the next steps. Also consider scheduling a debrief meeting with the testing team to walk through the report. This is your chance to ask questions and truly understand each finding, how difficult it was to exploit, what a real attacker could do with this, etc.
Step 7: Re-Test and Establish an Ongoing Testing Cycle
Once your review is complete, it is important to test some more and establish an ongoing testing cycle once your fixes are applied. Ideally, your penetration testing partner will include a follow-up test of the critical findings to confirm that vulnerabilities have been successfully remediated. For instance, if they found they could breach a web app via SQL injection, after you fix the code, they will try that attack again to ensure it’s truly resolved. Once everything is verified, you have a baseline of security.
Cybri: Your Partner for HIPAA and Healthcare Penetration Testing
As we discussed, healthcare penetration testing is rich in many aspects. Security expertise, understanding of healthcare’s unique landscape, and a sensitive approach that considers patient safety and compliance. After looking at the challenges and steps above, you may be interested in finding a suitable partner. This is where Cybri comes in.
At Cybri, we have deep pen testing healthcare sector experience. Our approach checks all the boxes we’ve outlined in this guide, such as deep healthcare compliance expertise (e.g., HIPAA, HITRUST, and HITECH frameworks), highly qualified professionals, and a light-touch testing process.
Strengthening Healthcare Security with Cybri Penetration Testing
Our US-based team ensures patient safety and uptime through a transparent, disruption-free process managed via our BlueBox PTaaS platform. And you receive comprehensive, actionable reports and remediation support tailored to your specific environment, from medical IoT to cloud apps, to not only pass audits but truly improve security.
Ready to fortify your healthcare cybersecurity? Get in touch with Cybri for a consultation. We can assess your needs and propose a penetration testing plan that fits your organization’s size, budget, and regulatory requirements. With Cybri’s support, you can confidently uncover hidden vulnerabilities before attackers do, strengthening your defenses and keeping your focus on delivering quality patient care.
Frequently Asked Questions
At a minimum, healthcare organizations should perform a full-scope penetration test once per year. Annual testing is recommended by industry best practices, and as of 2025, HHS is considering moving to yearly pen tests for HIPAA compliance [6]. Many organizations choose to test even more frequently or in a rolling fashion: for example, doing quarterly vulnerability scans plus targeted pen tests on different segments throughout the year.
A HIPAA Security Risk Assessment (SRA) is a broad evaluation required by HIPAA where an organization reviews all aspects of security risks to ePHI, including administrative, physical, and technical safeguards. It often involves checklists, policy reviews, and maybe high-level technical scanning. A penetration test, on the other hand, is a focused technical examination where testers actively try to exploit vulnerabilities in your systems.
When done correctly, penetration tests should not disrupt patient care. Professional penetration testing firms take extensive precautions to avoid impacting production systems. Engagements are planned in coordination with your IT team, for example, scheduling testing during low-usage periods or maintenance windows. Critical life-safety systems can be excluded from direct testing or only tested with passive methods.
When approached properly, penetration tests are about improving real security first and foremost, with compliance being a beneficial byproduct. It’s true that many healthcare organizations initially pursue pen testing to “check the box” for HIPAA, HITRUST, or a cybersecurity insurance requirement. But the true value comes in the security insights gained, as a penetration test will almost always uncover something that previously was unnoticed..
References
- Varonis. (April 2025). 38 Must-Know Healthcare Cybersecurity Stats
- IBM. (July 2024). Average Cost of a Healthcare Data Breach Increases to Almost $11 Million
- Medcrypt. (March 2025). Securing the Past to Protect the Future: Cybersecurity Best Practices for Legacy Medical Devices
- ScaleHub. (June 2024). Navigating a landscape of increasing healthcare data breaches
- Cybri. (n.d.). Does HIPAA Require Penetration Testing?
- Core Security. (July 2025). Proposed HIPAA Update Makes Yearly Pen Testing Mandatory














