Microsoft Azure is one of the world’s leading hyperscale cloud platforms, supporting everything from SaaS startups to global enterprises. In 2025, Microsoft announced that Azure generated “over $75 billion in annual revenue” [1]. This reflects the platform’s continued dominance in cloud computing, and is backed by industry data. Enterprise spending on cloud infrastructure services surpassed “$99 billion in Q2 2025” [2], marking another year of more than 25% growth.
Even with managed infrastructure, penetration testing remains critical. And Azure operates on a shared responsibility model. Microsoft secures the cloud infrastructure, while “customers are responsible for securing their own configurations, identities, data, and applications” [3]. Also, Azure penetration testing helps organizations proactively identify and remediate weaknesses across configurations, workloads, and connected applications before attackers exploit them.
What Is Azure Penetration Testing?
A controlled security assessment of the customer-managed portions of an Azure environment, including subscriptions, identities, data, and hosted applications, is referred to as Azure penetration testing. In practice, these tests operate under Microsoft’s shared responsibility framework, which clearly defines ownership boundaries.
As Microsoft explains: “We don’t perform penetration testing of your applications for you.” [4] Customers and their authorized testers must therefore assess the security of their own assets.
In contrast to traditional on-premises or application-only testing, Azure pentests must comply with Microsoft’s multi-tenant Rules of Engagement. Microsoft specifies: “The following guidelines present a cohesive framework for all forms of security testing, performed on Microsoft Online Assets.” [5] Certain risky activities, such as Denial-of-Service (DoS) or other destructive testing, are explicitly prohibited to prevent tenant-wide disruption.
Additionally, under Microsoft policy, customer-owned endpoints and workloads remain in scope, including web applications, APIs, and storage accounts. However, traffic that could disrupt services is not permitted. Microsoft clarifies that “one type of pen test you can’t perform is any kind of Denial-of-Service (DoS) attack.” [6] Instead, teams should evaluate DoS resilience through controlled simulations rather than live attacks.
Why Azure Environments Need Penetration Testing
Many cloud breaches stem from simple human error and weak configuration. According to Verizon’s 2025 DBIR, in error-driven breaches, “the top three action varieties were Misdelivery, Misconfiguration, and Publishing error.” [7] As a result, this highlights how easily attackers can exploit overlooked cloud controls. In particular, this risk becomes more significant in large, fast-changing Azure environments.
Common risks specific to Azure setups
- Over-permissive RBAC roles or unused service principals
- Misconfigured Network Security Groups (NSGs) exposing services to the internet
- Public or unencrypted storage accounts
- Weak Key Vault access controls or unmanaged secrets
- Gaps in Conditional Access or MFA coverage within Microsoft Entra ID
- Missing or ignored Defender for Cloud recommendations and monitoring gaps
- Insecure App Service, Function, or API deployments and CI/CD secrets
Penetration testing provides measurable assurance that supports major compliance frameworks. In this context, the AICPA defines SOC 2 as “a report on controls at a service organization relevant to security, availability, processing integrity, confidentiality, or privacy.” [8] Therefore, this level of assurance is what buyers expect from a mature Azure security program. Similarly, for healthcare workloads, HIPAA’s Security Rule requires organizations to “perform a periodic technical and nontechnical evaluation” [9] of safeguards. As a result, regular Azure testing helps satisfy these requirements by validating security controls in practice.
For SaaS companies handling enterprise data, regular Azure-focused testing reduces risk, streamlines vendor reviews, and builds trust with auditors. These benefits grow even stronger when findings are documented, remediated, and retested.
Scope of Azure Penetration Testing
An Azure penetration test focuses on the customer-controlled components of an Azure tenant. These typically include virtual machines, networking, hosted applications, APIs, cloud configurations, identity systems, and DevOps pipelines. In general, the assessment scope covers four main domains, each of which presents distinct risks that professional engagements should evaluate.

Azure Infrastructure
- Virtual Machines: exposed management ports, insecure OS configurations, missing updates, and weak remote access controls.
- Networking: public-facing load balancers, misrouted subnets, overly permissive Network Security Groups (NSGs), and misconfigured Application Gateway or WAF rules.
- Storage: publicly accessible Storage Accounts, containers with anonymous access, and missing encryption at rest or in transit.
- Operational controls: snapshot or backup exposure, insecure custom images, or credentials embedded in images.
- Practical guidance: apply the principle of least privilege to VM and identity assignments. Avoid long-lived keys or local credentials when managed identities are available. Microsoft recommends enforcing the “principle of least privilege for all role assignments.” [10]
Azure Applications and APIs
- Web applications: OWASP Top Ten risks such as XSS, SQL injection, and authentication flaws; insecure app settings that expose secrets; and public staging environments.
- Serverless and Functions: misconfigured bindings that expose function endpoints, weak input validation, and excessive permissions for function identities.
- API Management and Gateways: missing rate limits, weak CORS configurations, and lack of strong client authentication.
- Authentication and tokens: insecure token storage, long-lived refresh tokens, improper use of implicit flows, and missing token revocation mechanisms.
- API-level authorization: verify object-level checks. OWASP notes that “broken object level authorization is a leading API risk.” [11]
Azure Cloud Configurations
- Azure Active Directory (Entra ID): User accounts, conditional access policies, app registrations, and service principal permissions
- Storage Accounts: Blob/container permissions, encryption settings, public access levels, and shared access signatures
- Virtual Networks (VNet) & Network Security Groups (NSG): Network ACLs, firewall rules, peering configurations, and exposure to the internet
- Azure Functions & App Services: Authentication, authorization, managed identities, and function-level access controls
- Key Vault: Access policies, secret management, firewall rules, and RBAC assignments
- SQL Databases & Cosmos DB: Firewall rules, encryption at rest/transit, auditing, and connection string security
DevOps and CI/CD Pipelines
- Pipeline secrets: credentials, tokens, or service principals stored in plaintext within pipeline definitions or container images.
- Build and deploy integrity: unsigned artifacts, unscanned container images, or missing immutable promotion controls between environments.
- Insecure workflows: pipelines that execute arbitrary code with elevated privileges or push directly to production without review or approval.
The Azure Penetration Testing Process
A well-structured Azure penetration test follows a sequence that mirrors the attack lifecycle while staying within Microsoft’s approved testing boundaries. In practice, CYBRI, like other professional cloud security teams, applies a disciplined approach that ensures every finding is actionable and tied to business risk rather than only technical detail.
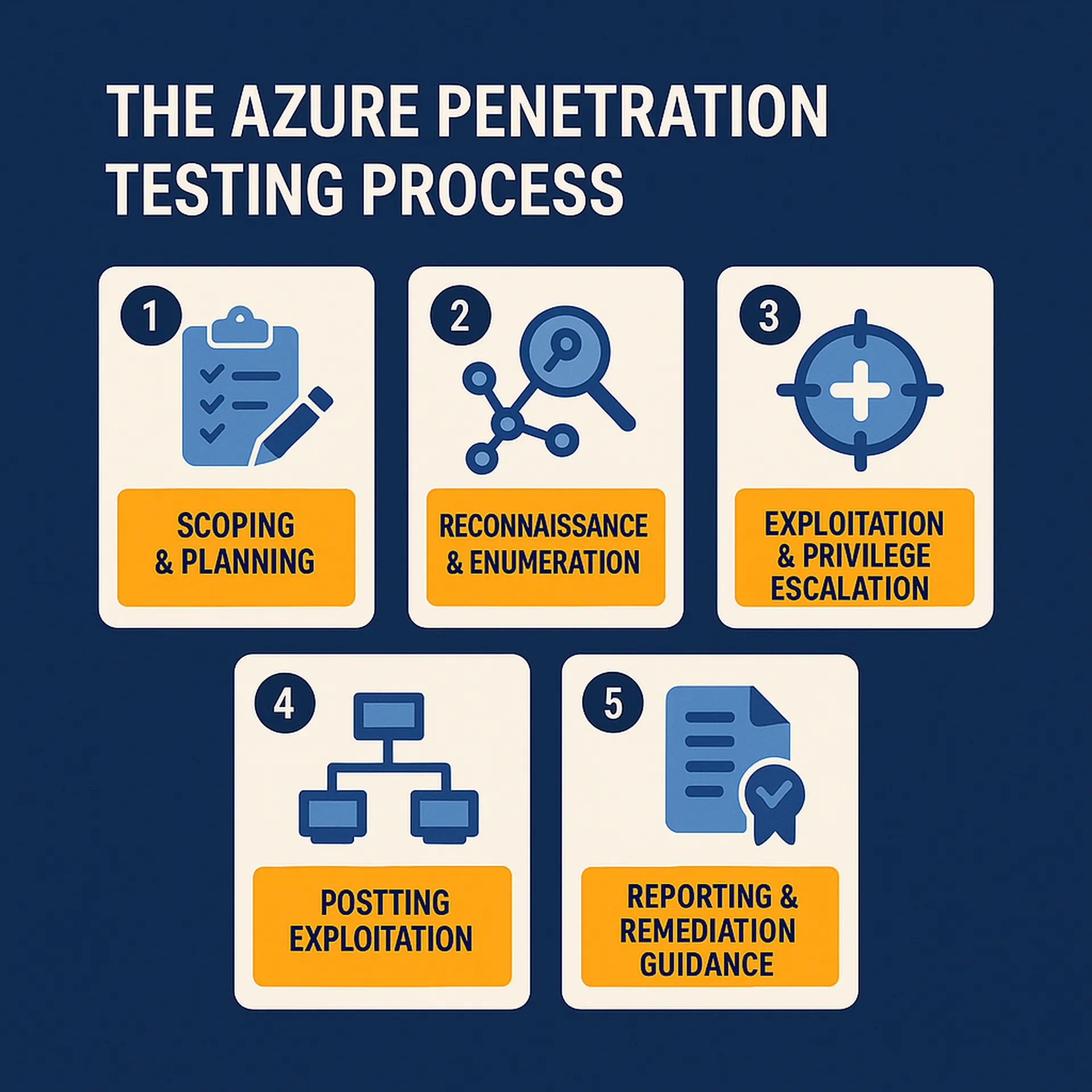
1. Scoping & Planning
Each engagement begins by defining the Azure assets, environments, and compliance objectives that fall within scope. This includes subscriptions, web applications, APIs, and infrastructure components. The planning phase ensures testing depth aligns with frameworks such as SOC 2, ISO 27001, and CIS Benchmarks, covering all relevant controls. Microsoft notes that “clearly defined scope and authorization are required before performing any security testing activities.”[12]
2. Reconnaissance & Enumeration
Testers map Azure resources, identify public endpoints, and enumerate metadata exposed to the internet. For example, common tasks include detecting misconfigured Network Security Groups (NSGs), open storage containers, and accessible App Service endpoints. In addition, automated discovery is combined with manual validation to confirm accuracy and reduce false positives.
3. Exploitation & Privilege Escalation
Once exposures are confirmed, testers attempt to exploit weak credentials, missing MFA enforcement, and privilege escalation paths in Microsoft Entra ID (Azure AD) or across subscriptions. Subsequently, they aim to safely demonstrate impact without disrupting operations. Microsoft guidance states that “penetration tests must avoid disruptive or destructive actions.” [13]
4. Post-Exploitation
This phase measures how far an attacker could move within the environment. Examples include accessing secrets in Azure Key Vault, sensitive databases, or pivoting through connected services. CYBRI’s testers simulate real-world attack chains while maintaining containment, traceability, and audit logging throughout the engagement.
5. Reporting & Remediation Guidance
The final deliverable includes an executive summary, technical findings, and remediation mapping aligned with Azure best practices. CYBRI stands out by providing actionable remediation guidance that links each issue to its fix, complete with Azure Portal or CLI examples and a built-in retest workflow through our PTaaS platform.
Key Tools and Techniques Used in Azure Penetration Testing
Effective Azure penetration tests combine targeted tooling with proven offensive techniques to uncover configuration flaws, identity weaknesses, and exploitable misconfigurations. In practice, the table below lists commonly used open-source tools and their typical purposes, followed by standard techniques used by professional testers.
| Tool | Purpose / Typical use |
| AzureHound | Collects data for BloodHound-style graphing of Azure and Entra relationships. In particular, it is used to map privileges, group membership, and delegated permissions during identity mapping. |
| MicroBurst | PowerShell toolkit for Azure discovery, blob enumeration, and weak-configuration checks. In addition, it is useful during reconnaissance and post-exploitation. |
| ROADrecon | AD Azure enumeration and analysis framework used to identify app registrations, consent grants, and potential attack paths. In addition, it helps identify app registrations, consent grants, and potential attack paths within an Azure environment. |
| AADInternals | PowerShell module for interacting with Microsoft Entra ID endpoints. In practice, it is commonly used to validate authentication flows and detect token-related weaknesses. |
| PowerZure | Automation and scripting toolkit for Azure enumeration and subscription-scope visibility. In addition, it is helpful for mapping service and resource access. |
Common techniques:
- Misconfiguration exploitation: locating permissive NSGs, public storage, or broad RBAC assignments that expose resources.
- Privilege escalation: chaining low-privilege accounts, exploiting app-consent misconfigurations, or modifying role assignments to gain elevated access.
- Access token hijacking and abuse: harvesting or misusing OAuth tokens, refresh tokens, or weakly protected service principal secrets.
- Credential attacks (password spraying, weak credentials): testing for weak or reused credentials across identities and service principals.
- Lateral movement and data-access validation: using compromised access to read or exfiltrate sensitive data such as blobs, databases, or configuration files that could impact business operations.
Common Vulnerabilities Found in Azure
Penetration testing in Azure frequently uncovers misconfigurations driven by convenience rather than control. In particular, one of the most common and critical issues is over-permissioned roles and users in Microsoft Entra ID (Azure AD). Microsoft advises that “it’s a best practice to grant users the least privilege to get their work done and avoid assigning broader roles at higher scopes.” [14]
Additionally, a second recurring vulnerability is unrestricted blob storage access. Datadog’s analysis shows that “58% of Azure Blob Storage containers were in storage accounts that proactively blocked public access in the latest period: up from 42% a year ago, which means 42% of containers still lacked that block.” [15] Meanwhile, “the share of containers that were effectively public declined to 1.3%, down from 2.6% a year earlier.” [16] These findings highlight that even small configuration oversights can expose critical business data to the internet.
Furthermore, weak or inconsistent Conditional Access enforcement, combined with missing MFA, often enables credential theft or session hijacking. The network layer presents additional risks as well. Testers frequently identify open management ports (SSH/RDP) and insecure VNet peering configurations that bypass segmentation controls.
Finally, Service Principal credentials, especially long-lived client secrets stored in code repositories or CI/CD pipelines, remain among the most exploited vectors for unauthorized privilege escalation in Azure environments.
Azure Penetration Testing for Compliance
Penetration testing for Azure is not only a security practice but also a compliance enabler. In addition, it verifies that controls operate effectively in real-world conditions. As a result, it provides evidence-based assurance that extends beyond documentation. Ultimately, this approach delivers measurable proof for several frameworks that are critical to SaaS and enterprise environments.
| Compliance Framework | Purpose of the Framework | How Azure Penetration Testing Supports It | Key Azure Focus Areas |
| SOC 2 (Type II) | Validates the operational effectiveness of controls related to security, availability, processing integrity, confidentiality, and privacy. | Confirms that security and confidentiality controls such as vulnerability management, change management, and incident response function effectively under testing. The AICPA notes that “SOC 2 reports are intended to meet the needs of a broad range of users that require detailed information about security and confidentiality controls” [8]. | Web application vulnerabilities, network configuration, data segregation, access control enforcement, remediation documentation. |
| ISO 27001:2022 | Establishes an Information Security Management System (ISMS) with ongoing risk assessment and control monitoring. | Serves as a recurring “risk evaluation and control validation” [17] activity, confirming that technical safeguards reduce identified risks. Testing supports compliance with Annex A (8.8) and (12.6). | Policies, least-privilege roles, encryption, configuration baselines, incident logging. |
| HIPAA (Security Rule) | Protects electronic protected health information (ePHI) across confidentiality, integrity, and availability safeguards. | Meets the “periodic technical evaluation” [9] requirement under 45 CFR §164.308(a)(8), verifying that Azure safeguards effectively protect ePHI in storage and in transit. | Key Vault protection of secrets, encryption in transit and at rest, access logging, workload segmentation, secure identity management. |
Choosing the Right Azure Penetration Testing Partner
Selecting the right provider for Azure workloads requires more than general cybersecurity experience. Instead, cloud environments demand specialists who understand the nuances of Azure identity, networking, and compliance.
What to Look For in an Azure Pentest Partner:
- Azure-specific expertise: The provider should demonstrate hands-on experience with Azure-native services such as App Service, Functions, Key Vault, Storage, Defender, and Entra ID. General web application knowledge is not enough. Familiarity with cloud roles, policies, and APIs is essential.
- Certified, cloud-literate testers: Seek teams with certifications such as OSCP, OSCE, CREST, or proven Azure Red Team and DevSecOps experience. These credentials show proficiency in exploitation, privilege escalation, and modern cloud security architecture.
- Compliance alignment: A capable partner should map findings to frameworks such as SOC 2, ISO 27001, or HIPAA, and clearly communicate remediation priorities that meet audit expectations.
- Transparent process and remediation support: The best firms deliver clear scoping, collaborative testing windows, and detailed remediation guidance, not just reports.
CYBRI’s senior ethical hackers specialize in Azure penetration testing. We help SaaS and enterprise teams identify vulnerabilities and strengthen compliance. Our PTaaS platform provides real-time collaboration with testers, live tracking of fixes, and retesting within the same engagement. This reduces downtime and ensures that every issue is validated before auditors review it.
Conclusion
Proactive Azure penetration testing is critical for maintaining a secure and resilient cloud environment. However, even within Microsoft’s ecosystem, customer-side misconfigurations, excessive permissions, and untested workloads continue to drive breaches. Therefore, regular testing verifies that security controls operate as intended, closing the gap between perceived and actual protection.
At CYBRI, every engagement is led by certified ethical hackers who understand Azure from the ground up. Our process combines clear communication, detailed reporting, and remediation-focused outcomes to help organizations strengthen compliance and security without slowing innovation.
If your business relies on Azure, ensure your security posture meets the same standard as your innovation. Contact us to schedule your Azure penetration test today.
Frequently Asked Questions
Yes. Microsoft allows testing of your own Azure resources, as long as you follow its Rules of Engagement and avoid disruptive actions like DoS attacks.
At least once a year, and after major updates or deployments.
A security assessment checks configurations; a penetration test actively exploits weaknesses to show real risk.
No. Microsoft secures the platform – you’re responsible for testing your own Azure workloads.
References
- Microsoft. (2025). Microsoft Annual Report 2025
- Synergy Research Group. (2025, July 31). Q2 Cloud Market Nears $100 Billion Milestone – and It’s Still Growing by 25% Year over Year
- Microsoft Learn. (2024, September 29). Shared responsibility in the cloud – Azure
- Microsoft Learn. (2025, April 23). Penetration testing
- Microsoft. (2025). Microsoft Security Testing Rules of Engagement
- Microsoft Learn. (2025, March 17). Tutorial: Azure DDoS Protection simulation testing
- Verizon. (2025). 2025 Data Breach Investigations Report (SMB Snapshot)
- AICPA. (2025). SOC 2 – SOC for Service Organizations (Trust Services Criteria)
- U.S. Department of Health & Human Services. (2024). 45 CFR §164.308 – Administrative safeguards (Security Rule)
- Microsoft. (2024). Azure Security Benchmark – guidance for securing Azure resources
- OWASP Foundation. (2019). OWASP API Security Top 10
- Microsoft Learn. (2024, May 12). Plan and authorize penetration testing in Azure
- Microsoft. (2025). Rules of Engagement for Security Testing
- Microsoft Learn. (2025). Best practices for Azure RBAC
- Datadog. (2024). The State of Cloud Security 2024
- International Organization for Standardization. (2022). ISO/IEC 27001:2022 Information security, cybersecurity and privacy protection – Information security management systems – Requirements














