Many startup founders reassure themselves with the phrase “We’re too small to be hacked.” Cybercriminals see it differently. Early-stage companies often store sensitive data, rely on cloud infrastructure, and operate without dedicated security staff. This makes them attractive and easy targets. Verizon’s 2025 Data Breach Investigations Report found that “43% of all breaches involved small and medium-sized businesses,” [1] proving that attackers don’t discriminate by company size.
A single security incident early in a company’s life cycle can have lasting consequences, including data exposure, downtime, and investor distrust. For startups that depend on customer confidence and rapid growth, one breach can threaten survival. IBM’s Cost of a Data Breach Report 2025 found that “organizations with fewer than 500 employees experienced an average data breach cost of $3.3 million,” [2] a figure that could instantly derail a startup’s runway.
Beyond financial loss, breaches can jeopardize compliance standing and block future funding. The U.S. Cybersecurity and Infrastructure
Security Agency (CISA) notes that “cybersecurity is not just an IT issue; it’s a business survival issue for small and midsize companies.” [3] For founders, early penetration testing is both a security measure and an investment in longevity. It uncovers exploitable weaknesses, prevents regulatory issues, and strengthens the trust needed to scale securely.
Common Security Challenges Startups Face
Even the most promising startups encounter recurring security challenges. These issues often stem from speed, small teams, and complex tech stacks. The points below highlight the most common barriers and why they matter.
- Rapid product development: Shipping features quickly often leaves little time for security planning or incident readiness. A small-business study found that “54% of small businesses don’t have a plan in place for reacting to cyberattacks,” [4] showing how easily security gets deprioritized as teams scale.
- Limited in-house security expertise: Early-stage teams usually lack dedicated security staff. The Cybersecurity and Infrastructure Security Agency (CISA) notes that “small businesses have valuable information that cybercriminals seek and often have fewer resources dedicated to cybersecurity.” [4] This imbalance makes day-to-day defense and incident response inconsistent.
- Reliance on third-party tools, APIs, and cloud infrastructure: Integrations and cloud services increase capability but also expand the attack surface. As research shows, “misconfigured cloud services are common targets for cyber actors.” [6] So, regular configuration reviews and access controls are essential.
- Compliance and investor due diligence: As sales cycles bring in enterprise customers or regulated industries, startups are asked to produce SOC 2 or ISO 27001 evidence, recent test results, and remediation proof. Delays in providing these artifacts can slow deals and raise governance concerns.
- Secrets sprawl and credential exposure: Rapid development, CI/CD pipelines, and SaaS integrations can lead to hard-coded credentials or tokens in code and build logs. This increases the risk of account takeover or lateral movement if secrets are leaked or reused.
Summary: Fast iteration, lean staffing, and rising compliance expectations create a perfect storm for early-stage teams. Proactive penetration testing helps detect exploitable flaws, validate cloud and API security, and provide credible assurance for customers, investors, and auditors.
Why Penetration Testing is Critical for Startups
Penetration testing gives early-stage companies a practical way to measure and improve real security: not just policy maturity. The sections below explain why it matters now.
Preventing Breaches and Downtime
Penetration tests uncover exploitable weaknesses before attackers do. As NIST defines it, “penetration testing is security testing in which assessors mimic real-world attacks to identify methods for circumventing the security features of an application, system, or network.” [6] Detecting and fixing these issues early reduces the likelihood of outages, data loss, and customer churn.
Building Trust with Customers and Investors
Security validation shortens sales cycles and strengthens investor confidence. Cisco’s global benchmark study found that “our customers won’t buy from us if their data is not properly protected,” [7] underscoring how security assurance influences purchasing decisions. A recent third-party penetration test also signals proactive risk management, helping startups establish credibility with enterprise buyers and capital partners.
Meeting Compliance Requirements
Many frameworks require or strongly encourage penetration testing, and buyers increasingly expect it even when not mandated. The PCI DSS guide states: “Develop and implement a methodology for penetration testing that includes external and internal penetration testing at least annually and after any significant upgrade or modification.” [8] Startups in sectors such as payments, healthcare, or finance often need recent test reports during procurement to satisfy due diligence and minimize audit friction.
Enabling Secure Growth
Every new feature, integration, or cloud change expands the attack surface. Testing before major launches and after significant architectural updates creates a repeatable checkpoint that keeps risk aligned with product velocity. Early testing prevents small flaws from compounding as the company scales.
When Should Startups Conduct a Penetration Test?
Security priorities evolve as a startup matures from Seed → Growth → Scale-up → Enterprise. At each stage, testing helps prevent small flaws from escalating into serious risks.
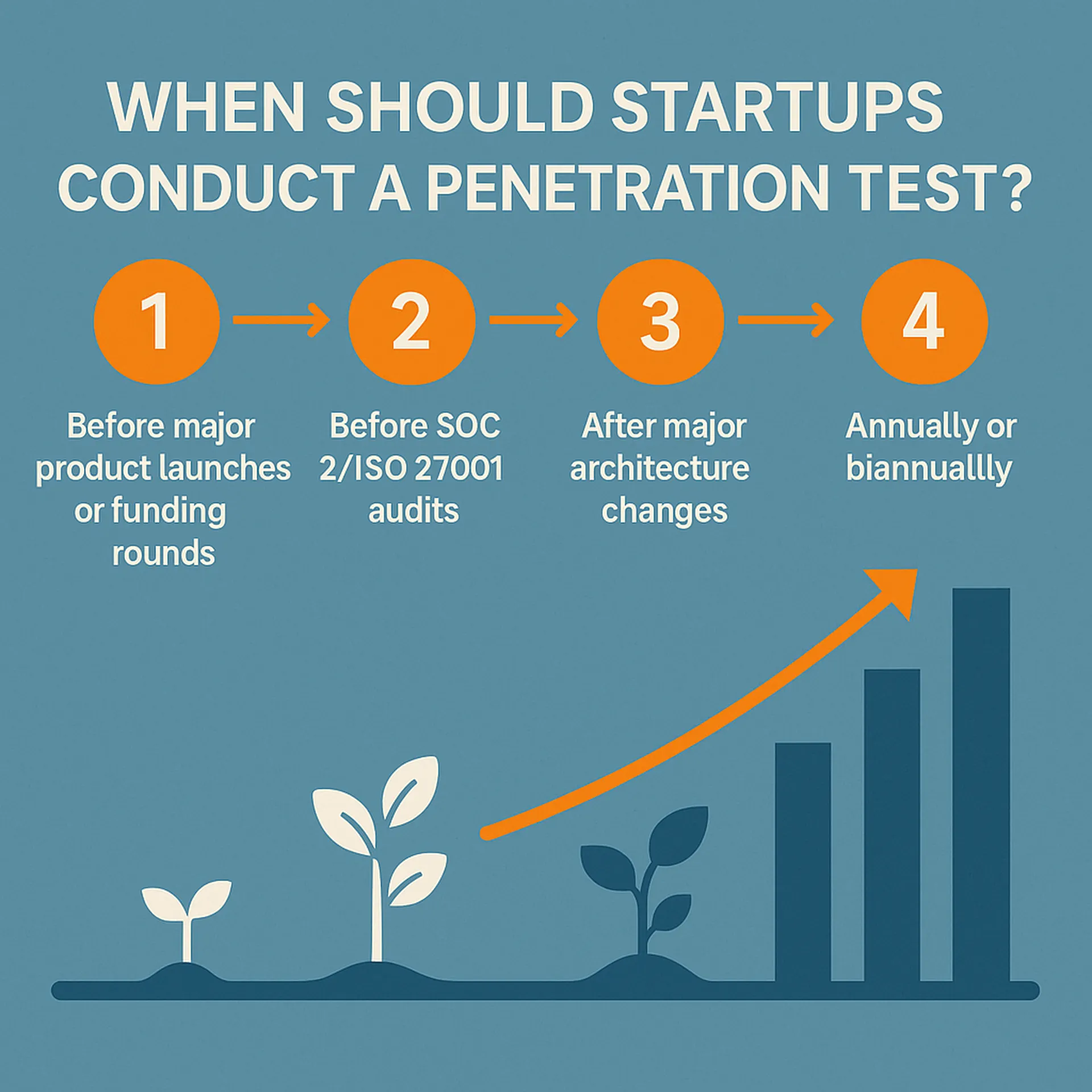
- Before major product launches or funding rounds: Validate releases before customers or investors encounter issues. Most breaches stem from preventable causes like human error, weak credentials, or social engineering. Verizon’s 2025 Data Breach Investigations Report found that “82% of breaches involved human error, misuse of privileges, stolen credentials, or social engineering.” [9] Testing at this stage prevents downtime, reputational harm, and investor hesitation.
- Before SOC 2 or ISO 27001 audits: Enterprise buyers expect verifiable security proof. The AICPA explains that “testing controls for design and operating effectiveness is critical to meet the trust services criteria for security and confidentiality.” [10] Conducting a pre-audit test confirms control strength and minimizes audit delays.
- After major architecture changes: New APIs, cloud migrations, or CI/CD redesigns can introduce new attack paths. AWS reminds users that “security and compliance are shared responsibilities, and changes to your architecture may require reassessment to maintain compliance.” [11] Testing after these events ensures new builds remain secure
- Annually or biannually: Regular testing keeps pace with growth. The Cybersecurity and Infrastructure Security Agency (CISA) advises small businesses to “conduct regular vulnerability and penetration testing to validate defenses and identify weaknesses before adversaries do.” [12] Establishing this cadence maintains compliance and demonstrates progress to customers and auditors.
Types of Penetration Tests Startups Should Consider
Different penetration tests target different layers of risk. Most startups begin with Application, API, and Cloud assessments bundled together, since these areas handle customer data and business-critical workloads. The table below summarizes each type, its purpose, and when to use it.
| Type of Test | Purpose | Common Findings | When to Use It |
| Application Penetration Testing | Examine web and mobile applications for exploitable flaws that affect customers or business logic. | Broken authentication, injection flaws, insecure session management, weak access control. | Before major product launches, feature releases, or compliance audits. |
| API Penetration Testing | Evaluate the security of APIs and integrations connecting apps, services, and third-party tools. | Excessive data exposure, missing authentication, broken object-level authorization. | Whenever APIs are added or exposed to partners or customers. |
| Cloud Penetration Testing | Assess AWS, GCP, or Azure environments for configuration and access risks. | Publicly accessible storage (for example, S3 buckets), overly permissive IAM roles, misconfigured VPCs or security groups. AWS reminds users that “security and compliance are shared responsibilities.” [13] | After new deployments, migrations, or significant infrastructure changes. |
| Internal & External Network Testing | Identify weaknesses in internal networks or perimeter-facing systems. | Open ports, unpatched systems, weak VPN configurations, exposed admin panels. | Annually, or after infrastructure expansion. |
| LLM and AI Penetration Testing | Examine AI and machine learning systems for data leakage, prompt injection, or model manipulation. | Sensitive prompt disclosure, insecure API endpoints, model poisoning. | When deploying AI components or integrating with external LLM APIs. |
Startups typically begin with App + API + Cloud testing to validate customer-facing systems and core infrastructure before adding internal or AI assessments.
Cybri helps SaaS companies prioritize these tests by mapping them to business risk and compliance goals, ensuring that early security investments deliver measurable impact.
How to Choose a Pen Testing Partner as a Startup

Step 1. Prioritize human expertise over tool output
Ask about methodology and request a sample report. A capable provider should explain how they test, how they validate findings, and how remediation is handled. NIST defines effective testing programs as efforts that “assist organizations in planning and conducting technical information security tests, analyzing findings, and developing mitigation strategies.”[14]
Step 2. Insist on stack alignment
Choose engineers experienced with systems similar to yours, such as React or Node.js front ends, APIs, and AWS architectures. OWASP calls its testing guide “a framework of best practices used by penetration testers and organizations worldwide,” [15] which provides a shared language when evaluating their approach and deliverables.
Step 3. Verify certifications and practical skill
Look for hands-on credentials that demonstrate real exploitation ability. Certifications such as OSCP, OSCE, and CISSP are widely recognized. These require testers to successfully exploit live systems in controlled lab environments, proving both technical accuracy and persistence.
Step 4. Confirm remediation guidance and retesting
Ask for clear, prioritized fixes and a defined retest window for High and Critical findings. A partner that includes retesting turns the report into a measurable improvement plan and gives you verified evidence for buyers and auditors.
Step 5. Demand transparent scoping and pricing
Request an itemized scope with defined environments, assumptions, deliverables, SLAs, and retest policy. Startup-friendly fixed packages make it easier to forecast costs and avoid hidden add-ons.
Step 6. Evaluate communication and access
Ensure you can speak directly with the assigned tester rather than only through tickets. Fast communication reduces remediation time, which is critical during launches or audits.
Step 7. Ask for relevant references or redacted samples
Review how the provider structures executive summaries, technical findings, and remediation guidance. Compare two vendors side by side using the same evaluation criteria to see who delivers clearer, more actionable results.
What a Startup Can Expect from the Pen Testing Process
Penetration testing follows a structured, collaborative flow. For startups, understanding each phase helps keep projects on schedule and ensures results are actionable.
- Scoping and goal alignment: Define what is in scope, such as applications, APIs, cloud assets, or internal systems, and clarify why the test is being conducted. This may include pre-launch validation, audit preparation, or investor assurance. The PCI Security Standards Council advises teams to “clearly define the scope of the test, including boundaries, constraints, and testing methods, to ensure complete and accurate coverage.” [16]
- Testing execution (manual and automated): Automated tools detect known flaws, while human testers validate results and explore complex attack paths. According to PCI DSS, “penetration testing complements vulnerability scanning by validating the effectiveness of security controls and the exploitability of identified vulnerabilities.” [16]
- Detailed report with risk prioritization: Expect an executive summary for leadership and detailed technical findings for engineers. Each issue should include severity, impact, and remediation steps. Reports must describe each issue clearly so that both technical and non-technical readers can make informed decisions.
- Remediation guidance and retesting: Engineers fix findings and testers re-validate them. This confirms that the environment is secure and that no new vulnerabilities were introduced. Verified remediation gives startups credible proof of progress for customers, auditors, and investors.
Typical Deliverables:
- Executive Summary (risk overview)
- Technical Findings (evidence, details, fixes)
- Proofs of Exploitation
- Remediation Tracker and Retest Report
These deliverables provide startups with actionable fixes and formal evidence of security maturity.
How Penetration Testing Supports Funding and Compliance

Penetration testing is not only a technical safeguard but also a visible sign of business maturity. For startups, it bridges the gap between security assurance and market credibility.
A verified penetration test report shows investors that the company manages risk seriously. In recent years, cybersecurity has become a standard part of funding due diligence. When founders present an independent test report, it reassures investors that both their product and operations are built on a secure foundation. This minimizes the perception of hidden risks and strengthens confidence during fundraising.
The same principle applies to enterprise customer onboarding. Large organizations now evaluate the security posture of their vendors before signing contracts. The World Economic Forum reports that “over 60% of organizations now include cybersecurity risk ratings and testing evidence in their vendor onboarding process.” [17] A verified test provides that evidence, reducing friction in sales cycles and helping startups move through procurement faster.
Penetration testing also supports compliance frameworks such as SOC 2, HIPAA, and ISO 27001. These audits require proof that controls work as intended, not just documentation. The AICPA notes that “penetration testing provides evidence of the operating effectiveness of security and confidentiality controls.” [18] Running a test before an audit gives teams time to correct findings and approach reviews with confidence.
Security maturity also influences mergers and acquisitions. Buyers now treat cybersecurity as a key part of valuation. A report by Infosys found that “53% of organizations have encountered a cybersecurity issue during M&A due diligence that jeopardized the deal.” [19] When vulnerabilities are found late, deals may be delayed, re-priced, or canceled. Cybri’s M&A-focused testing practice helps growth-stage SaaS companies prepare for this scrutiny by validating security ahead of acquisition and maintaining confidence during negotiations.
In short, penetration testing acts as an early-stage trust accelerator. It reassures investors, accelerates enterprise deals, simplifies compliance, and strengthens a startup’s position during fundraising or acquisition.
Conclusion: Security as a Startup Advantage
For startups, security is not a cost but a competitive advantage. Investing early in penetration testing reduces the risk of breaches, accelerates deals, and builds lasting trust with investors, customers, and auditors. Each engagement validates both technical defenses and organizational maturity.
The most successful startups embed security into their DNA from the beginning rather than adding it later. Treating penetration testing as a recurring checkpoint during launches, audits, and funding rounds helps founders scale with confidence while protecting valuation and reputation.
Cybri helps funded startups build secure and compliant foundations through tailored penetration testing and actionable remediation guidance. Get a free scoping consultation today.
References
- Verizon. (2025). Data Breach Investigations Report
- IBM. (2025). Cost of a Data Breach Report 2025
- Cybersecurity and Infrastructure Security Agency. (n.d.). Small and Medium Businesses
- Igniting Business. (2024). 10 Small Business Cyber Security Statistics
- Cybersecurity and Infrastructure Security Agency. (2022). Weak Security Controls and Practices Routinely Exploited for Initial Access
- National Institute of Standards and Technology. (2008). NIST SP 800-115: Technical Guide to Information Security Testing and Assessment
- Cisco. (2025). Data Privacy Benchmark Study
- PCI Security Standards Council. (2019). PCI DSS v3.2.1 Quick Reference Guide
- Verizon. (2024). Data Breach Investigations Report
- American Institute of CPAs (AICPA). (2022). Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy
- Amazon Web Services. (2023). Shared Responsibility Model
- Cybersecurity and Infrastructure Security Agency (CISA). (2024). Cybersecurity Guidance for Small and Medium-Sized Businesses
- Amazon Web Services. (2023). Shared Responsibility Model
- National Institute of Standards and Technology. (2008). NIST SP 800-115: Technical Guide to Information Security Testing and Assessment
- OWASP. (n.d.). Web Security Testing Guide
- PCI Security Standards Council. (2019). Penetration Testing Guidance v1.1
- World Economic Forum. (2025). Global Cybersecurity Outlook 2025
- American Institute of CPAs (AICPA). (2022). Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy
- Infosys. (2025). Cybersecurity Due Diligence in M&A: Identifying and Mitigating Risk Before the Deal














